- Craft and Criticism
- Fiction and Poetry
- News and Culture
- Lit Hub Radio
- Reading Lists
- Literary Criticism
- Craft and Advice
- In Conversation
- On Translation
- Short Story
- From the Novel
- Bookstores and Libraries
- Film and TV
- Art and Photography
- Freeman’s
- The Virtual Book Channel
- Behind the Mic
- Beyond the Page
- The Cosmic Library
- The Critic and Her Publics
- Emergence Magazine
- Fiction/Non/Fiction
- First Draft: A Dialogue on Writing
- The History of Literature
- I’m a Writer But
- Lit Century
- Tor Presents: Voyage Into Genre
- Windham-Campbell Prizes Podcast
- Write-minded
- The Best of the Decade
- Best Reviewed Books
- BookMarks Daily Giveaway
- The Daily Thrill
- CrimeReads Daily Giveaway

Word Are Deeds: Rebecca Solnit the Power of Speech to Shape the Future
“your opponents would love you to believe that it’s hopeless, that you have no power.”, our 21 most-anticipated sci-fi, fantasy, and horror books for the rest of 2024, books for the witches, spacefarers, and ghouls among us, “it’s harder for me to talk about them.” percival everett on the paintings he makes, j.c. gabel talks to the acclaimed novelist and poet about his latest art exhibition, the literary film & tv you need to stream in july, for staying inside, from shopping to sex: indexing the life of sylvia plath, carl rollyson on the revelations and limits of a quantitative exercise, teenage queen: behind the scenes on the set of my lady jane, alexis gunderson on bringing the little told story of lady jane grey to the screen, generation franchise: why writers are forced to become brands (and why that’s bad), jess row on the ubiquity of the digital persona, from child stars to disney adults, in search of the rarest book in american literature: edgar allan poe’s tamerlane, bradford morrow on the bibliophile’s holy grail, otherwise known as the “black tulip”, 75 years of 1984 : why george orwell’s classic remains more relevant than ever, elif shafak on the relentless real-world spread of orwellian dystopia, a book club of two: the time i started a james joyce reading group in college, kristopher jansma on the special magic of reading “ulysses”, the worst dads in all of literature: an incomplete list, garth risk hallberg on the dysfunctional fathers of the western canon, the ultimate summer 2024 reading list, or, beach book bingo, what jane austen’s work can tell us about the british imperial project, corinne fowler considers the colonial legacy of the english countryside, ten debut lgbtq+ authors on the books that shaped them as writers, jiaming tang, jessie ren marshall, brittany rogers, alana saab and many more reflect on their formative texts, rebecca solnit: the loneliness of donald trump, on the corrosive privilege of the most mocked man in the world, the literary film & tv you need to stream in june, summertime, and the streaming’s easy, 18 new novels you need to read this summer, more light, more books, remembering paul auster, ursula k. le guin on how to become a writer, (step one: write), here’s your 2024 literary film & tv preview, 53 shows and movies to stream and see this year, lit hub’s most anticipated books of 2024, 230 books we’re looking forward to reading this year, 24 sci-fi and fantasy books to look forward to in 2024, exciting new series’ and standalones from kelly link, lev grossman, sofia samatar, james s.a. corey, and more, we need your help: support lit hub, become a member, you get editors’ personalized book recs, an ad-free reading experience, and the joan didion tote bag, gaza diaries: “we left our souls at home.”.
From Heba Al-Agha’s Account of the last Eight Months of Israel’s War on Gaza (trans. Julia Choucair Vizoso)

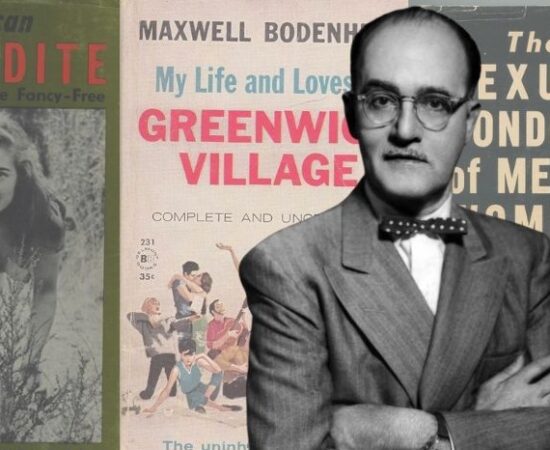
Remembering Samuel Roth, the Bookseller Who Defied America’s Obscenity Laws
Ed Simon on Free Speech, Book Bans and Court-Mandated Censorship, Then and Now
New York, New York: On Getting By As an Artist In the City That Never Sleeps
Marin Kosut Considers the Romanticized Myths That Underpin Countless Artistic Dreams

Seeking a Gentler Mythology of the American West
Joe Wilkins on His Grandfather, the Sheeprancher

Joseph O’Neill on Writing a Socially Relevant Soccer Novel
Belinda McKeon Talks to the Author of “Godwin”

Where There's Smoke... How Wildfires Across North America Are Making Children Sick
Debra Hendrickson Considers the Impact of Climate Change on Her Career as a Pediatrician

July 3, 2024
- Ross Gay on the small joy of listening to the Fugees in a coffee shop
- Joshua Bodwell remembers Neeli Cherkovski
- Looking back at the books honored (and overlooked) at the National Book Awards
to the Lithub Daily
Support lit hub..

Lit hub Radio
News, Notes, Talk

Daily Fiction
From Pink Slime
The God of the Woods
From the god of the woods.
Prairie Edge

Support One Moment, Racism the Next: On Being a Black Nigerian Man in America

How Do We Balance the Needs of the Earth With the Needs of Humanity?
How white sharks became the serial killers of the sea.
John Long on the Hunting Tactics of One of Nature's Most Feared Predators

10 Great New Children’s Books to Throw in Your Beach Bag

What Working at Restaurants Can Teach Writers

The Best Reviewed Books of the Month

5 Reviews You Need to Read This Week

Ram Murali's 10 Favorite Agatha Christie Short Stories

On Secret Societies, Dark Academia, and Blending the Real with the Unreal
- RSS - Posts
Literary Hub
Created by Grove Atlantic and Electric Literature
Sign Up For Our Newsletters
How to Pitch Lit Hub
Advertisers: Contact Us
Privacy Policy
Support Lit Hub - Become A Member

Literary Criticism: Critical Analysis on the Web
- Articles & Databases
- Books & E-Books
- Critical Analysis on the Web
- Citing & Writing
- Locating Course Readings
Trusted Websites
Online Literary Criticism contains biographical and citical information collected by librarians.
English Literature on the Web contains links to author pages, journals, magazines and websites dedicated to English-language literature.
New York Times Book Reviews Search the New York Times for book reviews from 1981 to the present.
Global Shakespeare is a collaborative project providing online access to performances of Shakespeare from many parts of the world as well as essays and metadata by scholars and educators in the field.
Poetry Archives is a large collection of English-language poetry from around the world.
Cambridge History of English and American Literature contains over 300 chapters with essay topics ranging from poetry, fiction, drama and essays to history, theology and political writing.
- LitCharts.com Small but growing site of literature guides for works commonly used in high school and college classes.
- Poetry Writing and Analysis Guide This site, managed by a company called SuperSummary, has basic information about how to critically read and analyze poetry.
Material from Google Scholar
Google Scholar searches the web for scholarly material. Search for the author or title of the work along with some search terms that relate to your research question to find academic articles.
Found a great article but you cannot access it? Request the article through interlibrary loan and we'll send you a copy.

Use your RADAR to Evaluate the Source
The RADAR framework provides criteria to help you evaluate the quality, credibility, and relevance of any source of information. Keep these questions in mind when considering if you should use a source in your assignment.
R elevance - is the information/source important to my specific topic or research question?
A uthority - was it written by a credible expert? What institution are they affiliated with?
D ate - when was the source published or last updated? Is it a current article (past 10 years)?
A ppearance - does it look like a research article? Is there methods/results section?
R eason - why was the information produced in the first place? Who was it written for?
- << Previous: Books & E-Books
- Next: Citing & Writing >>
- Last Updated: Jul 3, 2024 3:09 PM
- URL: https://libguides.sait.ca/literary_criticism
Chat with Us

- Privacy Policy

Home » Critical Analysis – Types, Examples and Writing Guide
Critical Analysis – Types, Examples and Writing Guide
Table of Contents

Critical Analysis
Definition:
Critical analysis is a process of examining a piece of work or an idea in a systematic, objective, and analytical way. It involves breaking down complex ideas, concepts, or arguments into smaller, more manageable parts to understand them better.
Types of Critical Analysis
Types of Critical Analysis are as follows:
Literary Analysis
This type of analysis focuses on analyzing and interpreting works of literature , such as novels, poetry, plays, etc. The analysis involves examining the literary devices used in the work, such as symbolism, imagery, and metaphor, and how they contribute to the overall meaning of the work.
Film Analysis
This type of analysis involves examining and interpreting films, including their themes, cinematography, editing, and sound. Film analysis can also include evaluating the director’s style and how it contributes to the overall message of the film.
Art Analysis
This type of analysis involves examining and interpreting works of art , such as paintings, sculptures, and installations. The analysis involves examining the elements of the artwork, such as color, composition, and technique, and how they contribute to the overall meaning of the work.
Cultural Analysis
This type of analysis involves examining and interpreting cultural artifacts , such as advertisements, popular music, and social media posts. The analysis involves examining the cultural context of the artifact and how it reflects and shapes cultural values, beliefs, and norms.
Historical Analysis
This type of analysis involves examining and interpreting historical documents , such as diaries, letters, and government records. The analysis involves examining the historical context of the document and how it reflects the social, political, and cultural attitudes of the time.
Philosophical Analysis
This type of analysis involves examining and interpreting philosophical texts and ideas, such as the works of philosophers and their arguments. The analysis involves evaluating the logical consistency of the arguments and assessing the validity and soundness of the conclusions.
Scientific Analysis
This type of analysis involves examining and interpreting scientific research studies and their findings. The analysis involves evaluating the methods used in the study, the data collected, and the conclusions drawn, and assessing their reliability and validity.
Critical Discourse Analysis
This type of analysis involves examining and interpreting language use in social and political contexts. The analysis involves evaluating the power dynamics and social relationships conveyed through language use and how they shape discourse and social reality.
Comparative Analysis
This type of analysis involves examining and interpreting multiple texts or works of art and comparing them to each other. The analysis involves evaluating the similarities and differences between the texts and how they contribute to understanding the themes and meanings conveyed.
Critical Analysis Format
Critical Analysis Format is as follows:
I. Introduction
- Provide a brief overview of the text, object, or event being analyzed
- Explain the purpose of the analysis and its significance
- Provide background information on the context and relevant historical or cultural factors
II. Description
- Provide a detailed description of the text, object, or event being analyzed
- Identify key themes, ideas, and arguments presented
- Describe the author or creator’s style, tone, and use of language or visual elements
III. Analysis
- Analyze the text, object, or event using critical thinking skills
- Identify the main strengths and weaknesses of the argument or presentation
- Evaluate the reliability and validity of the evidence presented
- Assess any assumptions or biases that may be present in the text, object, or event
- Consider the implications of the argument or presentation for different audiences and contexts
IV. Evaluation
- Provide an overall evaluation of the text, object, or event based on the analysis
- Assess the effectiveness of the argument or presentation in achieving its intended purpose
- Identify any limitations or gaps in the argument or presentation
- Consider any alternative viewpoints or interpretations that could be presented
- Summarize the main points of the analysis and evaluation
- Reiterate the significance of the text, object, or event and its relevance to broader issues or debates
- Provide any recommendations for further research or future developments in the field.
VI. Example
- Provide an example or two to support your analysis and evaluation
- Use quotes or specific details from the text, object, or event to support your claims
- Analyze the example(s) using critical thinking skills and explain how they relate to your overall argument
VII. Conclusion
- Reiterate your thesis statement and summarize your main points
- Provide a final evaluation of the text, object, or event based on your analysis
- Offer recommendations for future research or further developments in the field
- End with a thought-provoking statement or question that encourages the reader to think more deeply about the topic
How to Write Critical Analysis
Writing a critical analysis involves evaluating and interpreting a text, such as a book, article, or film, and expressing your opinion about its quality and significance. Here are some steps you can follow to write a critical analysis:
- Read and re-read the text: Before you begin writing, make sure you have a good understanding of the text. Read it several times and take notes on the key points, themes, and arguments.
- Identify the author’s purpose and audience: Consider why the author wrote the text and who the intended audience is. This can help you evaluate whether the author achieved their goals and whether the text is effective in reaching its audience.
- Analyze the structure and style: Look at the organization of the text and the author’s writing style. Consider how these elements contribute to the overall meaning of the text.
- Evaluate the content : Analyze the author’s arguments, evidence, and conclusions. Consider whether they are logical, convincing, and supported by the evidence presented in the text.
- Consider the context: Think about the historical, cultural, and social context in which the text was written. This can help you understand the author’s perspective and the significance of the text.
- Develop your thesis statement : Based on your analysis, develop a clear and concise thesis statement that summarizes your overall evaluation of the text.
- Support your thesis: Use evidence from the text to support your thesis statement. This can include direct quotes, paraphrases, and examples from the text.
- Write the introduction, body, and conclusion : Organize your analysis into an introduction that provides context and presents your thesis, a body that presents your evidence and analysis, and a conclusion that summarizes your main points and restates your thesis.
- Revise and edit: After you have written your analysis, revise and edit it to ensure that your writing is clear, concise, and well-organized. Check for spelling and grammar errors, and make sure that your analysis is logically sound and supported by evidence.
When to Write Critical Analysis
You may want to write a critical analysis in the following situations:
- Academic Assignments: If you are a student, you may be assigned to write a critical analysis as a part of your coursework. This could include analyzing a piece of literature, a historical event, or a scientific paper.
- Journalism and Media: As a journalist or media person, you may need to write a critical analysis of current events, political speeches, or media coverage.
- Personal Interest: If you are interested in a particular topic, you may want to write a critical analysis to gain a deeper understanding of it. For example, you may want to analyze the themes and motifs in a novel or film that you enjoyed.
- Professional Development : Professionals such as writers, scholars, and researchers often write critical analyses to gain insights into their field of study or work.
Critical Analysis Example
An Example of Critical Analysis Could be as follow:
Research Topic:
The Impact of Online Learning on Student Performance
Introduction:
The introduction of the research topic is clear and provides an overview of the issue. However, it could benefit from providing more background information on the prevalence of online learning and its potential impact on student performance.
Literature Review:
The literature review is comprehensive and well-structured. It covers a broad range of studies that have examined the relationship between online learning and student performance. However, it could benefit from including more recent studies and providing a more critical analysis of the existing literature.
Research Methods:
The research methods are clearly described and appropriate for the research question. The study uses a quasi-experimental design to compare the performance of students who took an online course with those who took the same course in a traditional classroom setting. However, the study may benefit from using a randomized controlled trial design to reduce potential confounding factors.
The results are presented in a clear and concise manner. The study finds that students who took the online course performed similarly to those who took the traditional course. However, the study only measures performance on one course and may not be generalizable to other courses or contexts.
Discussion :
The discussion section provides a thorough analysis of the study’s findings. The authors acknowledge the limitations of the study and provide suggestions for future research. However, they could benefit from discussing potential mechanisms underlying the relationship between online learning and student performance.
Conclusion :
The conclusion summarizes the main findings of the study and provides some implications for future research and practice. However, it could benefit from providing more specific recommendations for implementing online learning programs in educational settings.
Purpose of Critical Analysis
There are several purposes of critical analysis, including:
- To identify and evaluate arguments : Critical analysis helps to identify the main arguments in a piece of writing or speech and evaluate their strengths and weaknesses. This enables the reader to form their own opinion and make informed decisions.
- To assess evidence : Critical analysis involves examining the evidence presented in a text or speech and evaluating its quality and relevance to the argument. This helps to determine the credibility of the claims being made.
- To recognize biases and assumptions : Critical analysis helps to identify any biases or assumptions that may be present in the argument, and evaluate how these affect the credibility of the argument.
- To develop critical thinking skills: Critical analysis helps to develop the ability to think critically, evaluate information objectively, and make reasoned judgments based on evidence.
- To improve communication skills: Critical analysis involves carefully reading and listening to information, evaluating it, and expressing one’s own opinion in a clear and concise manner. This helps to improve communication skills and the ability to express ideas effectively.
Importance of Critical Analysis
Here are some specific reasons why critical analysis is important:
- Helps to identify biases: Critical analysis helps individuals to recognize their own biases and assumptions, as well as the biases of others. By being aware of biases, individuals can better evaluate the credibility and reliability of information.
- Enhances problem-solving skills : Critical analysis encourages individuals to question assumptions and consider multiple perspectives, which can lead to creative problem-solving and innovation.
- Promotes better decision-making: By carefully evaluating evidence and arguments, critical analysis can help individuals make more informed and effective decisions.
- Facilitates understanding: Critical analysis helps individuals to understand complex issues and ideas by breaking them down into smaller parts and evaluating them separately.
- Fosters intellectual growth : Engaging in critical analysis challenges individuals to think deeply and critically, which can lead to intellectual growth and development.
Advantages of Critical Analysis
Some advantages of critical analysis include:
- Improved decision-making: Critical analysis helps individuals make informed decisions by evaluating all available information and considering various perspectives.
- Enhanced problem-solving skills : Critical analysis requires individuals to identify and analyze the root cause of a problem, which can help develop effective solutions.
- Increased creativity : Critical analysis encourages individuals to think outside the box and consider alternative solutions to problems, which can lead to more creative and innovative ideas.
- Improved communication : Critical analysis helps individuals communicate their ideas and opinions more effectively by providing logical and coherent arguments.
- Reduced bias: Critical analysis requires individuals to evaluate information objectively, which can help reduce personal biases and subjective opinions.
- Better understanding of complex issues : Critical analysis helps individuals to understand complex issues by breaking them down into smaller parts, examining each part and understanding how they fit together.
- Greater self-awareness: Critical analysis helps individuals to recognize their own biases, assumptions, and limitations, which can lead to personal growth and development.
About the author
Muhammad Hassan
Researcher, Academic Writer, Web developer
You may also like

Graphical Methods – Types, Examples and Guide

Documentary Analysis – Methods, Applications and...

Table of Contents – Types, Formats, Examples

Problem Statement – Writing Guide, Examples and...

Research Techniques – Methods, Types and Examples

Data Verification – Process, Types and Examples
Literary Analysis Maker
The literary analysis maker is an AI-powered online tool that can generate literary analysis in just a few seconds! It can help college and high school students with literary criticism assignments, saving time and effort. In addition, our generator can help students improve their literary analysis skills and serve as a source of inspiration!
Try our literary analysis maker right now to see how it works!
- ✒️ What Is Literary Analysis?
- 💫 Tool Benefits
- 💡 Ideas for Literary Analysis
- ✍️ Literary Analysis Prompts
- 📋 Literary Analysis Structure
🔗 References
✒️ what does literary analysis mean.
Literary analysis is a written evaluation of the elements of a literary work, for example, a poem, short story, novel, etc. It aims to deepen one's understanding of the work's ideas and impact on the readers.
Literary analysis is not just about summarizing what you read . It involves deconstructing the artwork to evaluate its parts, including plot, character, setting, theme, style, and symbolism. This assignment provides an opportunity to learn more about the underlying meanings of a literary work and see how its elements help the author convey the intended message.
💫 Literary Analysis Maker: Benefits
The literary analysis essay writer has a lot of benefits for its users. Check the table below to learn more!
| 🧠 Smart | Our literary analysis essay generator is based on AI algorithms, allowing you to get original and customized results. |
|---|---|
| ⏱️ Fast | Simply fill in the details and click the button, and the result will appear within several seconds. |
| 💡 Stimulating | The tool provides users with inspirational ideas and allows them to take a fresh look at a literary work. |
| 🔁 Unlimited | You can use the literary analysis maker as many times as you need. |
| 💸 Free | You do not have to spend any money to use our tool since it is 100% free! |
💡 What to Write a Literary Analysis on?
If you are wondering what to write a literary analysis on, do not panic! Below, we've listed all the important elements of literary analysis with brief instructions on how to evaluate them.
| Characters | Summarize how the author describes the characters. Then, identify whether the characters are , flat or round, or representative of some universal quality. Another way is to compare and contrast two characters. |
|---|---|
| Setting | Analyze the relationship between the work's setting and its mood, theme, and characters. Consider how the setting impacts the characters' actions and interactions. |
| Plot | Examine the work's beginning, suspense, , flashbacks, cause-effect relationships, and logical order. Examine events leading to climax and resolution. |
| Theme | Investigate the work's central theme and how the author conveys it. Identify the literary devices used, symbols, and allusions that support the theme. Determine the significance of the work's title in relation to the theme. |
| Imagery | Analyze the in the text to determine its significance and how it contributes to the work's meaning and overall impact. Identify how these images are interrelated with other literary elements. |
| Figures of speech | Examine how such as similes, metaphors, and hyperboles are used throughout the text. Explore how these figures of speech intertwine with other literary elements. |
| Rhyme & rhythm | If you're analyzing poetry, identify the rhyme scheme and rhythm pattern throughout the text and its impact on the author's message. Analyze how the author employs different rhymes and rhythms as sound devices for the literary work. |
✍️ Literary Analysis Essay Prompts
Looking for some inspiration? You are on the right page! Check our writing prompts on literary analysis to find a lot of fresh ideas!
To Kill a Mockingbird Literary Criticism Essay
In your essay on To Kill a Mockingbird , you can discover and analyze autobiographical elements. Note how Harper Lee uses characters like Atticus Finch and Scout in her novel to reflect experiences from her own life, particularly surrounding discrimination, racism, and rape. Discuss how the novel's setting, historical context, symbolism, and imagery reinforce Lee's core message.
Hamlet Literary Analysis Essay
To write a good analysis of Shakespeare's Hamlet , investigate dialogues, soliloquies, and the play's vivid and rich language filled with rhetorical devices . You can devote particular attention to such literary devices as allusion and metaphors and add your point of view on the impact of Hamlet on the audience.
The Great Gatsby Literary Criticism Essay
Analyze the significance of the clock in F. Scott Fitzgerald's The Great Gatsby as a symbol of time, focusing on its multi-faceted meaning and its impact on the characters and themes. Discuss how the clock represents Gatsby's attempt to control time and its connection to his ultimate fate.
A Raisin in the Sun Literary Analysis Essay
In a literary analysis essay on A Raisin in the Sun , you can analyze the theme of dreams in this novel. Discuss the characters of Ruth, Lena, Travis, Beneatha, and Walter, focusing on the personal dreams they yearn to achieve. Evaluate how the Younger family's dreams are affected by social, economic, and emotional circumstances.
Lord of the Flies Literary Analysis Essay
In your essay, analyze William Golding's portrayal of human nature in Lord of the Flies , focusing on the influence of the environment on people's behavior. Examine the character developments of Ralph, Jack, Simon, and others, revealing their experiences on an island that show both good and evil potential within each individual.
📋 How to Structure a Literary Analysis
The structure of literary criticism consists of 3 key parts: the introduction, main body, and conclusion. Check the table below to see what to include in each part.
| Introduction | . focusing on a specific literary element. |
|---|---|
| Main body | indicating what the paragraph will be about. with a transition to the next paragraph. |
| Conclusion |
❓ Literary Analysis Free: FAQ
Updated: Mar 28th, 2024
- Discovering Evidence for a Literary Analysis Essay – San José State University Writing Center
- Writing about Literature – Fordham University
- Literary Criticism – UTA Libraries
- Writing Your Literary Analysis – University of Hawaii
- Literary Analysis – Appalachian State University
- Free Essays
- Writing Tools
- Lit. Guides
- Donate a Paper
- Referencing Guides
- Free Textbooks
- Tongue Twisters
- Job Openings
- Video Contest
- Writing Scholarship
- Discount Codes
- Brand Guidelines
- IvyPanda Shop
- Online Courses
- Terms and Conditions
- Privacy Policy
- Cookies Policy
- Copyright Principles
- DMCA Request
- Service Notice
Our literary analysis maker will help you break down any piece of literature! Get a detailed review of the plot, narrative techniques, and other text elements in a few clicks. Additionally, read the guide to discover excellent literary analysis prompts and examples.

Literary Research: Find Websites
- Getting Started
- Find Articles
- Find Websites
- Additional Help
Need Help Searching?

- The Research Process Research Guide
- Evaluating Information
Some Words on Online Literary Guides
Online guides, such as Sparknotes or CliffsNotes , have a nice amount of summary and background, but take the time to evaluate their quality.
Use these sites as a reference and not as cited sources in your essay. They are no substitute for your own critical reading of the text or literary criticism found in scholarly journals or books.
Literary Websites
Explore the following website for primary and secondary works along with useful information about literary criticism.
- The Academy of American Poets Find biographies on and poems by your favorite poets. The site also includes video, audio, and author interviews.
- Purdue Online Writing Lab Resources on writing literary essays. Topics include writing about fiction or poetry, literary theory, and literary terms.
- The Literature Network Allows you to search for primary texts, such as short stories, poems, and novels. Also includes author biographies.
- Project Gutenberg Over 36,000 eBooks available to download. Search for literary works and primary texts.
- Poetry Foundation Browse poems by title, author, or time period. Site also contains interviews, articles, and podcasts.
- The Paris Review Search the archive by author name or decade for author interviews.
Google Scholar
Use Google Scholar for a preliminary search. Don't forget to check the library and library databases for titles you may find through Google Scholar! Many scholarly works still remain unavailable on the web.
| |
- << Previous: Find Articles
- Next: Additional Help >>
- Columbus State Community College
- Research Guides
- Literary Research
- Last Updated: Jan 16, 2024 10:37 AM
- URL: https://library.cscc.edu/literature
- Staff Login

Privacy & Confidentiality Statement Library Code of Conduct
Explore all things Literature
Any Book. Any Author. Understand them all.
Used by 4 Million+ People
Join the Best Literature Community
Great for Students, Teachers, Readers, Book Fanatics and more!
Create Your Personal Profile
Engage in Forums
Join Special Interest Groups
Create your own groups, save your favorites, explore books picked by experts.
Discover 166 books with in-depth analysis and reviews written by experts.

Stephen King
Of Mice and Men

John Steinbeck
Catcher in the Rye

J.D. Salinger
The Great Gatsby

F. Scott Fitzgerald

George Orwell

Neil Gaiman
Explore any Author
Discover 122 authors with in-depth analysis & reviews written by experts.

Explore all 603 Book Terms
Understand Books at the Deepest Level with our Glossary. Click on any book to unveil all the terms.
Expand terms list

Frank Herbert
Game of thrones.

George R.R. Martin
Harry potter.

J.K. Rowling
The hunger games.

Suzanne Collins
Our latest books.
Not sure where to start? Here are the latest books from our Literature Experts.

Unlock the World of Literature with Book Analysis. Our expert team dives deep into the literary realm to bring you comprehensive summaries and analyses. From students to book lovers, we have something for everyone.
Request a Book
Can’t find a specific book that you are looking for? Request it here and we take care of the rest.
More Than Just Books. We’re committed to making a difference in the world.

Teenage Cancer Trust

Alzheimer’s Research

Great Ormond Street Hospital
Ocean conservancy.

World Animal Protection
There was a problem reporting this post.
Block Member?
Please confirm you want to block this member.
You will no longer be able to:
- See blocked member's posts
- Mention this member in posts
- Invite this member to groups
Please allow a few minutes for this process to complete.
Critically Analyzing Information Sources: Critical Appraisal and Analysis
- Critical Appraisal and Analysis
Initial Appraisal : Reviewing the source
- What are the author's credentials--institutional affiliation (where he or she works), educational background, past writings, or experience? Is the book or article written on a topic in the author's area of expertise? You can use the various Who's Who publications for the U.S. and other countries and for specific subjects and the biographical information located in the publication itself to help determine the author's affiliation and credentials.
- Has your instructor mentioned this author? Have you seen the author's name cited in other sources or bibliographies? Respected authors are cited frequently by other scholars. For this reason, always note those names that appear in many different sources.
- Is the author associated with a reputable institution or organization? What are the basic values or goals of the organization or institution?
B. Date of Publication
- When was the source published? This date is often located on the face of the title page below the name of the publisher. If it is not there, look for the copyright date on the reverse of the title page. On Web pages, the date of the last revision is usually at the bottom of the home page, sometimes every page.
- Is the source current or out-of-date for your topic? Topic areas of continuing and rapid development, such as the sciences, demand more current information. On the other hand, topics in the humanities often require material that was written many years ago. At the other extreme, some news sources on the Web now note the hour and minute that articles are posted on their site.
C. Edition or Revision
Is this a first edition of this publication or not? Further editions indicate a source has been revised and updated to reflect changes in knowledge, include omissions, and harmonize with its intended reader's needs. Also, many printings or editions may indicate that the work has become a standard source in the area and is reliable. If you are using a Web source, do the pages indicate revision dates?
D. Publisher
Note the publisher. If the source is published by a university press, it is likely to be scholarly. Although the fact that the publisher is reputable does not necessarily guarantee quality, it does show that the publisher may have high regard for the source being published.
E. Title of Journal
Is this a scholarly or a popular journal? This distinction is important because it indicates different levels of complexity in conveying ideas. If you need help in determining the type of journal, see Distinguishing Scholarly from Non-Scholarly Periodicals . Or you may wish to check your journal title in the latest edition of Katz's Magazines for Libraries (Olin Reference Z 6941 .K21, shelved at the reference desk) for a brief evaluative description.
Critical Analysis of the Content
Having made an initial appraisal, you should now examine the body of the source. Read the preface to determine the author's intentions for the book. Scan the table of contents and the index to get a broad overview of the material it covers. Note whether bibliographies are included. Read the chapters that specifically address your topic. Reading the article abstract and scanning the table of contents of a journal or magazine issue is also useful. As with books, the presence and quality of a bibliography at the end of the article may reflect the care with which the authors have prepared their work.
A. Intended Audience
What type of audience is the author addressing? Is the publication aimed at a specialized or a general audience? Is this source too elementary, too technical, too advanced, or just right for your needs?
B. Objective Reasoning
- Is the information covered fact, opinion, or propaganda? It is not always easy to separate fact from opinion. Facts can usually be verified; opinions, though they may be based on factual information, evolve from the interpretation of facts. Skilled writers can make you think their interpretations are facts.
- Does the information appear to be valid and well-researched, or is it questionable and unsupported by evidence? Assumptions should be reasonable. Note errors or omissions.
- Are the ideas and arguments advanced more or less in line with other works you have read on the same topic? The more radically an author departs from the views of others in the same field, the more carefully and critically you should scrutinize his or her ideas.
- Is the author's point of view objective and impartial? Is the language free of emotion-arousing words and bias?
C. Coverage
- Does the work update other sources, substantiate other materials you have read, or add new information? Does it extensively or marginally cover your topic? You should explore enough sources to obtain a variety of viewpoints.
- Is the material primary or secondary in nature? Primary sources are the raw material of the research process. Secondary sources are based on primary sources. For example, if you were researching Konrad Adenauer's role in rebuilding West Germany after World War II, Adenauer's own writings would be one of many primary sources available on this topic. Others might include relevant government documents and contemporary German newspaper articles. Scholars use this primary material to help generate historical interpretations--a secondary source. Books, encyclopedia articles, and scholarly journal articles about Adenauer's role are considered secondary sources. In the sciences, journal articles and conference proceedings written by experimenters reporting the results of their research are primary documents. Choose both primary and secondary sources when you have the opportunity.
D. Writing Style
Is the publication organized logically? Are the main points clearly presented? Do you find the text easy to read, or is it stilted or choppy? Is the author's argument repetitive?
E. Evaluative Reviews
- Locate critical reviews of books in a reviewing source , such as the Articles & Full Text , Book Review Index , Book Review Digest, and ProQuest Research Library . Is the review positive? Is the book under review considered a valuable contribution to the field? Does the reviewer mention other books that might be better? If so, locate these sources for more information on your topic.
- Do the various reviewers agree on the value or attributes of the book or has it aroused controversy among the critics?
- For Web sites, consider consulting this evaluation source from UC Berkeley .
Permissions Information
If you wish to use or adapt any or all of the content of this Guide go to Cornell Library's Research Guides Use Conditions to review our use permissions and our Creative Commons license.
- Next: Tips >>
- Last Updated: Jun 21, 2024 3:08 PM
- URL: https://guides.library.cornell.edu/critically_analyzing
Mobile Menu
- Find a Tutor
- Connection User
- Edit Profile
- Forgot Password
- Novelguides by Title
- Reports & Essay by Title
- Quotes by Author
- Novelguides by Author
- Ask a Question
- Novelguides
- Connections
- Reports & Essays
- Ask Question
- Tutor's Market Place
- How it Works
What are You Studying?
Novelguide rooms, novelguide: search by author, novelguide: search by title, latest novelguides.
- To Kill A Mockingbird Plot summary | Discussion & Questions
- The Great Gatsby Plot summary | Discussion & Questions
- Lord of the Flies Plot summary | Discussion & Questions
- Adventures of Huck Finn Plot summary | Discussion & Questions
- The Catcher in the Rye Plot summary | Discussion & Questions
- Animal Farm Plot summary | Discussion & Questions
- 1984 Plot summary | Discussion & Questions
- Fahrenheit 451 Plot summary | Discussion & Questions
- Odysseus Plot summary | Discussion & Questions
- Great Expectations Plot summary | Discussion & Questions
Latest Forum Topics
- Making a decision of career
- Exam preparation tips
- Learning Strategies
- Do It Yourself
- Teacher Different Teaching Tips
- Homeschooling
- Positive school climate
Top William Shakespeare's Novels
- Hamlet Plot summary | Discussion & Questions
- Henry IV Part 1 Plot summary | Discussion & Questions
- Julius Caesar Plot summary | Discussion & Questions
- As You Like It Plot summary | Discussion & Questions
- Macbeth Plot summary | Discussion & Questions
- Othello Plot summary | Discussion & Questions
- Romeo and Juliet Plot summary | Discussion & Questions
- The Merchant of Venice Plot summary | Discussion & Questions
- Much Ado About Nothing Plot summary | Discussion & Questions
- All's Well That Ends Well Plot summary | Discussion & Questions
Free Study Guide Answers, Book and Literature Notes - Novelguide.com
find your school by states.
Quotes By Topic
Report & essay.
- Thomas Jefferson: the Man, the Myth, and the Morality
- JFK: His Life and Legacy
- Gerald Ford
- Harry Shippe Truman
- Herbert Hoover
- The Presidency of FDR
- J.F.K. Biography
- James Madison
"Love one another and you will be happy. It's as simple and as difficult as that."

Quotes: Search By Author
Search reports and essays.
Novelguide.com is the premier free source for literary analysis on the web. We provide an educational supplement for better understanding of classic and contemporary literature. Novelguide.com is continually in the process of adding more books to the website each week. Please check back weekly to see what we have added. Please let us know if you have any suggestions or comments or would like any additional information. Thanks for checking out our website. More Details
Our Networks
- novelguide.com
- studyhall.novelguide.com
- Homework Help
- flashcard.novelguide.com/
- video.novelguide.com
- Share Report & Essay
- Join a school
- Join a teacher group
- Test Prep Material
Useful Links
- See what's new on our blog
- All Question
- Novelguide Authors
- Search Your School
- Teacher ratings
Literary Theory and Criticism

Scopus-indexed Journals English Language, Literature, and Cultural Studies
By NASRULLAH MAMBROL on May 30, 2024
Here is an updated list of Scopus-indexed journals focusing on English Language, Literature, and Cultural Studies S. No. Journal Title ISSN Publisher Quartile 1 Men and Masculinities 1097184X SAGE Publications Inc. Q1 2 3 4 Poetics 0304422X Elsevier Q1 5… Read More ›
Recent Posts
English poetry in the sixteenth century.
By NASRULLAH MAMBROL on July 17, 2020 • ( 0 )

The poetry of the sixteenth century defies facile generalizations. Although the same can obviously be said for the poetry of other periods as well, this elusiveness of categorization is particularly characteristic of the sixteenth century. It is difficult to pinpoint… Read More ›
Analysis of John Milton’s Paradise Lost
By NASRULLAH MAMBROL on July 12, 2020 • ( 0 )

Paradise Lost is a poetic rewriting of the book of Genesis. It tells the story of the fall of Satan and his compatriots, the creation of man, and, most significantly, of man’s act of disobedience and its consequences: paradise was… Read More ›
Join One Year Online Coaching for NTA UGC NET JRF English
By NASRULLAH MAMBROL on July 7, 2020 • ( 0 )

Join ONE YEAR Online Coaching for NTA UGC NET JRF English Conducted by Literariness.org BATCH 2 Coaching for December 2020 and June 2021 English NET Exam. Features 📌 No Time Constraints 📌 Printable materials in pdf 📌 Life-time access to the… Read More ›
Analysis of T.S. Eliot’s Love Song of J. Alfred Prufrock
By NASRULLAH MAMBROL on July 5, 2020 • ( 0 )

No poet in memory has ever had quite so spectacular a debut as the young T. S. Eliot when his poem The Love Song of J. Alfred Prufrock was first published in Poetry magazine in 1915, thanks in large part… Read More ›
Analysis of T.S. Eliot’s The Waste Land
By NASRULLAH MAMBROL on July 4, 2020 • ( 0 )

Nothing could have prepared either the literary world in general or the curious reader who had been following Eliot’s career to date for the publication, in late 1922, of The Waste Land. Published in October of that year in Eliot’s… Read More ›
A Brief History of American Novels
By NASRULLAH MAMBROL on June 27, 2020 • ( 0 )

America became a subject for literature after the Revolutionary War, when writers began the exploration of themes and motifs distinctly American. Continuing the Puritan belief in America as the New Eden, writers stressed the millennial nature of settlement and progress…. Read More ›
A Brief History of English Literature
By NASRULLAH MAMBROL on July 18, 2018 • ( 14 )

CHAPTER 1 OLD ENGLISH LITERATURE The Old English language or Anglo-Saxon is the earliest form of English. The period is a long one and it is generally considered that Old English was spoken from about A.D. 600 to about 1100…. Read More ›
Analysis of Tahar Ben Jelloun’s The Sacred Night
By NASRULLAH MAMBROL on May 21, 2024

Tahar Ben Jelloun in The Sacred Night depicts Moroccan society and rails against social injustice, sexual and religious hypocrisy, gender inequalities, patriarchy, and women’s oppression. He conveys his social critique in a poetic and concise style blending realism with dreamlike… Read More ›
Analysis of Ngugi wa Thiong’o’s The River Between
By NASRULLAH MAMBROL on March 27, 2024

The River Between is the first novel, though the second published work, by author Ngugi wa Thiong’o. The book represents a foray into the complex exploration of intracultural Gikuyu struggle expressed in the language of the English colonialist power that… Read More ›
Analysis of Miroslav Krleža’s The Return of Philip Latinovicz

The Return of Philip Latinovicz is the major fictional work of the Croatian novelist, playwright, poet, and essayist Miroslav Krleža (1893– 1981). Krleža, who was to become a preeminent cultural and political figure in post–World War II Yugoslavia, wrote his… Read More ›
Analysis of Rachid Boudjedra’s The Repudiation
By NASRULLAH MAMBROL on March 17, 2024

Rachid Boudjedra (1941– ) began writing in the 1960s, a period during which the Algerian novel in French shifted from a critique of colonialism to a questioning of social, political, and religious structures. Like most of the Algerian Francophone writers,… Read More ›
Analysis of Euclides da Cunha’s Rebellion in the Backlands
By NASRULLAH MAMBROL on March 10, 2024

One of the most significant cultural currents in the mid- to late 19th century was an increasing interest in defining national characteristics as part of the development of nationalism. In the Czech lands this activity took the form of a… Read More ›
Analysis of Camara Laye’s The Radiance of the King
By NASRULLAH MAMBROL on February 20, 2024

Originally published in French, The Radiance of the King is the most famous novel of Camara Laye (1928–80), whose name is sometimes listed as Laye Camara. In contrast with a number of early African novels that focused on an African… Read More ›
Analysis of Joseph Roth’s The Radetzky March

The Radetzky March, first published in Berlin in 1932, is regarded as the most significant novel by Joseph Roth (1894–1939) and the work that clearly defines the author’s public image as a Hapsburg nostalgist. Joseph Roth was born in Brody,… Read More ›
Analysis of P. P. Raveendran’s Literature as Supermarket: Mapping World Literature Today
By NASRULLAH MAMBROL on February 4, 2024

In his article ‘Literature as Supermarket: Mapping World Literature Today’, P. P. Raveendran reviews the genealogy of the concept of ‘World Literature’ to bring out the theoretical underpinnings of the term as it was used in different contexts and examines… Read More ›
Analysis of Terry Eagleton’s What is Literature

Terry Eagleton’s exploration of the definition of literature in his introduction to “What is Literature?” presents a multifaceted inquiry into the nature of literary discourse. Eagleton begins by questioning the very existence of literary theory, suggesting that if such a… Read More ›

Analysis of Stephen Greenblatt’s Introduction to The Power of Forms in the English Renaissance

Stephen Greenblatt is an American Literary critic. Greenblatt is one of the founders of New Historicism which is also known as cultural poetics. While he was teaching at the University of California, Berkeley, Greenblatt helped to found a journal called… Read More ›
Analysis of Mikhail Sholokhov’s Quiet Flows the Don
By NASRULLAH MAMBROL on January 6, 2024

Regarded as the definitive novel by Russian author Mikhail Sholokhov (1905–1984), Quiet Flows the Don was both a significant contribution to the corpus of work that earned Sholokhov the Nobel Prize in 1965 and a source of extensive and long-standing… Read More ›
Analysis of Khalil Gibran’s The Prophet
By NASRULLAH MAMBROL on October 4, 2023

The Prophet, by the Lebanese-American author Khalil Gibran, occupies a peculiar place in 20th-century world literature. The Prophet has been translated into more than 100 languages, making it one of the most translated books in history. By 2012, it had… Read More ›
Analysis of Miguel Ángel Asturias Rosales’s The President
By NASRULLAH MAMBROL on August 4, 2023

The most popular novel by Nobel Prize winner Miguel Ángel Asturias Rosales (1899–1974), The President is a classic of Latin American literature. The novel examines the political phenomenon of dictatorship by exploring the ways in which authoritarian regimes oppress subjects… Read More ›
Analysis of Albert Camus’s The Plague

The Plague was written by Albert Camus (1913–60), one of the most gifted and influential writers and philosophers in the French language of the 20th century. He was awarded the Nobel Prize in literature in 1957. Camus was born in… Read More ›
Analysis of Patrick Süskind’s Perfume: The Story of a Murderer
By NASRULLAH MAMBROL on August 3, 2023

The late 20th-century novel Perfume: The Story of a Murderer (Das Parfum. Die Geschichte eines Mörders) by Patrick Süskind (1949– ) is probably the best-known German literary text to appear in the last half of the century. It is a… Read More ›
Analysis of Juan Rulfo’s Pedro Páramo

Pedro Páramo was voted by literary critics in the Spanish newspaper El País (May 5, 2001) as the most important book written in Spanish in the 20th century. It is generally understood that the technique of the novel of the… Read More ›
Analysis of Władysław Reymont’s The Peasants

The Peasants is undoubtedly the greatest narrative achievement by the Polish author Władysław Reymont (1867–1925). The four volumes of the novel, titled after the four seasons, were serialized in a weekly magazine for nearly a decade and finally earned him… Read More ›
Analysis of André Gide’s The Pastoral Symphony

La symphonie pastorale, translated as The Pastoral Symphony (1931), but just as often called by its French title by English-speaking critics, is part of a group of firstperson narratives called récits. Récits are characterized by a simple and ironic text… Read More ›
Analysis of Karen Blixen’s Out of Africa

The Danish author Karen Blixen (1885–1962) wrote Out of Africa originally in English, publishing this novelistic memoir in Denmark, Sweden, and England in 1937, and in the United States in 1938. This was her second book, following Seven Gothic Tales…. Read More ›
- ‹ Older Entries
You must be logged in to post a comment.

- Cambridge Libraries
Study Skills
Critical analysis: home.
- Reading Critically
What is Critical Analysis?
Analysis is a word that is also often used when taking a critical approach to something. It could be that you look at some evidence and if you think it is good quality, you may choose to include that in your essay or writing to help support your argument. When you have analysed different sets of evidence you may synthesize all the ideas gathered from multiple sources bringing together the relevant information into a different argument or idea.
To evaluate something or someone, you think and consider it or them in order to make a judgment about it/them; this could be as simple as how good or bad they are. When you critically evaluate something or someone you consider how judgments vary from different perspectives and how some judgments are stronger than others. This often means creating an objective, reasoned argument for your overall case, based on the evaluation from different perspectives.
Taking a critical approach when you are studying involves constantly asking questions and keeping an open mind.
- Next: Reading Critically >>
- Last Updated: Aug 9, 2023 11:57 AM
- URL: https://libguides.cam.ac.uk/criticalanalysis
© Cambridge University Libraries | Accessibility | Privacy policy | Log into LibApps

Writing a Critical Analysis
What is in this guide, definitions, putting it together, tips and examples of critques.
- Background Information
- Cite Sources
Library Links
- Ask a Librarian
- Library Tutorials
- The Research Process
- Library Hours
- Online Databases (A-Z)
- Interlibrary Loan (ILL)
- Reserve a Study Room
- Report a Problem
This guide is meant to help you understand the basics of writing a critical analysis. A critical analysis is an argument about a particular piece of media. There are typically two parts: (1) identify and explain the argument the author is making, and (2), provide your own argument about that argument. Your instructor may have very specific requirements on how you are to write your critical analysis, so make sure you read your assignment carefully.

Critical Analysis
A deep approach to your understanding of a piece of media by relating new knowledge to what you already know.
Part 1: Introduction
- Identify the work being criticized.
- Present thesis - argument about the work.
- Preview your argument - what are the steps you will take to prove your argument.
Part 2: Summarize
- Provide a short summary of the work.
- Present only what is needed to know to understand your argument.
Part 3: Your Argument
- This is the bulk of your paper.
- Provide "sub-arguments" to prove your main argument.
- Use scholarly articles to back up your argument(s).
Part 4: Conclusion
- Reflect on how you have proven your argument.
- Point out the importance of your argument.
- Comment on the potential for further research or analysis.
- Cornell University Library Tips for writing a critical appraisal and analysis of a scholarly article.
- Queen's University Library How to Critique an Article (Psychology)
- University of Illinois, Springfield An example of a summary and an evaluation of a research article. This extended example shows the different ways a student can critique and write about an article
- Next: Background Information >>
- Last Updated: Jun 27, 2024 8:26 AM
- URL: https://libguides.pittcc.edu/critical_analysis
Your all in one AI-powered Reading Assistant
A Reading Space to Ideate, Create Knowledge, & Collaborate on Your Research
- Smartly organize your research
- Receive recommendations that can not be ignored
- Collaborate with your team to read, discuss, and share knowledge
From Surface-Level Exploration to Critical Reading - All at One Place!
Fine-tune your literature search.
Our AI-powered reading assistant saves time spent on the exploration of relevant resources and allows you to focus more on reading.
Select phrases or specific sections and explore more research papers related to the core aspects of your selections. Pin the useful ones for future references.
Our platform brings you the latest research news, online courses, and articles from magazines/blogs related to your research interests and project work.
Speed up your literature review
Quickly generate a summary of key sections of any paper with our summarizer.
Make informed decisions about which papers are relevant, and where to invest your time in further reading.
Get key insights from the paper, quickly comprehend the paper’s unique approach, and recall the key points.
Bring order to your research projects
Organize your reading lists into different projects and maintain the context of your research.
Quickly sort items into collections and tag or filter them according to keywords and color codes.
Experience the power of sharing by finding all the shared literature at one place
Decode papers effortlessly for faster comprehension
Highlight what is important so that you can retrieve it faster next time
Find Wikipedia explanations for any selected word or phrase
Save time in finding similar ideas across your projects
Collaborate to read with your team, professors, or students
Share and discuss literature and drafts with your study group, colleagues, experts, and advisors. Recommend valuable resources and help each other for better understanding.
Work in shared projects efficiently and improve visibility within your study group or lab members.
Keep track of your team's progress by being constantly connected and engaging in active knowledge transfer by requesting full access to relevant papers and drafts.
Find Papers From Across the World's Largest Repositories

Testimonials
Privacy and security of your research data are integral to our mission..
Everything you add or create on Enago Read is private by default. It is visible only if and when you share it with other users.
You can put Creative Commons license on original drafts to protect your IP. For shared files, Enago Read always maintains a copy in case of deletion by collaborators or revoked access.

We use state-of-the-art security protocols and algorithms including MD5 Encryption, SSL, and HTTPS to secure your data.

Gale Literature Criticism
Discover centuries of literary analysis.
Gale Literature Criticism , the award-winning series provides unparalleled access and navigation through centuries of literary analysis—spanning all time periods, genres, and regions of the world.
Gale Literature Criticism takes literature, history and culture to the next level with the largest, most extensive compilation of literary commentary available. The 10 award-winning series that comprise Gale Literature Criticism represent a range of modern and historical views on authors and their works across regions, eras and genres.
Imagine centuries of analysis—the scholarly and popular commentary from broadsheets, pamphlets, encyclopedias, books and periodicals—delivered in an easy-to-use online format that matches the exact look and content of the print originals. The net result is tens of thousands of hard-to-find essays at your fingertips. It's all designed to raise the level of research while providing the around-the-clock remote access that today's researchers demand.
View Brochure
View Fact Sheet
Contact Your Rep to Learn More
Gale Literature Criticism Resources
| Provides a wide variety of critical information with numerous entries focusing on topics in children’s and young adult literature, as well as picture books, folklore and graphic novels | Assembles critical responses to the works from every region of the world, from the earliest known examples of written works to the eve of the modern era. | For users seeking a deeper understanding of contemporary literature from the works of writers, novelists, philosophers, and political leaders from around the world. | Presents discerning commentary on dramatic works of enduring interest and introduce researchers to the most frequently studied playwrights of all time periods and nationalities. |
| Explores the works of writers, novelists, poets, playwrights, philosophers, political leaders, scientist, and mathematicians from the Late Medieval period through the age of colonial expansion | A valuable resource for students and librarians seeking critical commentary on writers of this transitional period. | For students and librarians seeking critical commentary and scholarly discourse on influential poems and the world’s most renowned poets. |
| A must-have resource for Shakespeare that provides researchers with multiple viewpoints, documenting the critical reaction of scholars and commentators from the 17th century to today. | Enables users to critically analyze the works of the most influential short story authors giving new context to classic fiction. | Fosters a deeper understanding of twentieth-century literature by providing your users with critical responses to the works of nearly 1,200 authors. |

The Ultimate Guide to Website Analysis (With Examples)
- Conversion Rate Optimization
Kobiruo Otebele
You most likely have a live website if you own an online business.
And considering the massive competition and the sheer number of online businesses, it feels so much like owning a storefront in the bustling city of the internet.
It’s safe to say having a website isn’t enough. Not even close.
You have to optimize it so that it attracts visitors and converts those visitors into customers by actually shopping from you.
But first, you have to conduct a website analysis to understand your target audience.
You’ll have to identify what’s stopping them from buying. Why are they bouncing off? The ones who are shopping—what’s making them shop?
Once you have an answer to all these whys and hows, you can optimize your website accordingly to cater to your target audience.
That’s what website analysis is all about—a diagnostic tool that not only identifies the issues but also provides actionable insights to optimize your online presence.
In this guide, we’ll discuss the nitty-gritty of website analysis, covering everything from customer-led analysis to behavior analytics, types of analysis, and the tools you need to get the job done.
We’ll also take a unique approach that focuses on customer-led website analysis to optimize a website for your customers rather than merely replicating what competitors are doing.
What is Website Analysis?
Website analysis is the process of examining and evaluating a site’s performance, design, content, and user experience to identify areas for improvement and optimize its effectiveness.
It’s like conducting a health check-up for your website, ensuring that it’s performing at its best and providing a great experience for your visitors.
Benefits Of Conducting A Website Analysis
Website analysis provides feedback on website performance and user experience. These two factors are vital to increasing leads and revenue, which is every business’s dream.
Here are some of the prominent benefits of website analysis.
- Website analysis reveals areas where you can improve and update your website.
- Your data and results can impact your strategies to get more visitors.
- Analyzing the competition’s website is not often discussed, but it can help you discover keywords and content to target and attract fresh visitors.
Key aspects and types of website analysis
When conducting a website analysis, you must optimize different areas to increase your website’s performance.
Here are some key aspects of website analysis you should know before starting the process:
1. SEO Analysis
This involves assessing the website’s visibility on search engines and its compliance with SEO best practices.
A typical SEO analysis will include:
- On-page SEO: Optimizing elements like titles, headings, meta descriptions, and content for targeted keywords.
- Off-page SEO: Analyzing backlinks and external factors that impact your website’s authority and rankings.
- Technical SEO: Checking your site’s technical aspects, like website speed, mobile-friendliness, and crawlability, to ensure they meet search engine standards.
- Local SEO: Analyzing your website’s visibility in local search results, which is crucial for businesses targeting local customers.
Pro Tip: To determine which elements are responsible for slow load times, there are free and paid tools you can use (Google Page Speed Insights, Pingdom).
Here are some tips to consider when conducting an SEO analysis:
- Find and add long-tail keywords: Your SEO strategy isn’t complete without long-tail keywords.
- Create a keyword map: A keyword map helps you discover where to optimize, what content to build, and where you can add new pages to attract more traffic.
- Generate and submit a sitemap: This will tell search engines which pages to crawl.
- Create a Robots.txt file: This makes it clear to search engines which pages shouldn’t be crawled.
- Use analytics tools: Set up Google Analytics, Search Console, and Bingmaster tools to get invaluable insights into your site performance.
2. Performance Analysis
This involves checking the website’s speed, loading times, and overall responsiveness.
After all, a fast-loading website is indispensable for keeping visitors engaged. For example, Google found that a one-second delay in mobile loading times can impact conversion rates by up to 20% .
3. CRO Analysis
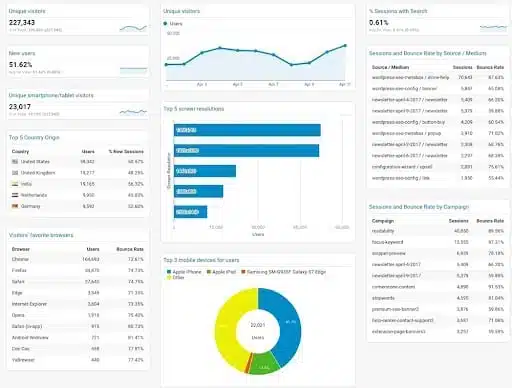
Conversion rate optimization audit involves taking a 360-degree approach to evaluating your website, identifying and eliminating conversion blockers, and increasing sales.
That said, CRO is a broad field. You need to focus on your traffic and messaging to succeed with your analysis.
Traffic here refers to website visitors who land on your site every day. A thorough CRO analysis starts with understanding how users interact with your site (their actions and behavior on your website).
You need tools that give you quantitative and qualitative insights to understand your traffic better.
Quantitative data refers to user behavior that can be measured and given a numerical value, e.g., number of visitors per page, session duration, bounce rate, etc.
To access this data type, you can use tools like Google Analytics, Open Web Analytics, Similarweb, etc.
Another crucial aspect of CRO audits is analyzing your website’s message to see how users respond.
Online shoppers don’t just land on a website out of the blue. They follow different touchpoints before finally being directed to your website—it could be through an ad, a simple Google search, or a blog post.
When conducting a CRO analysis of your website, you want to ensure that your website’s copy (on different pages) resonates with your target audience.
You can follow these tips when conducting a CRO analysis for your website:
- Define key conversion goals: You need to have a goal, e.g., reducing cart abandonment on checkout, etc.
- Focus on priority pages: don’t be carried away by conducting an audit on pages that don’t drive conversions. Focus on pages where the money is, e.g., product and category pages, etc.
- Understand user behavior: Conduct user research by launching polls and surveys, using analytics, going through session recordings and heat maps, etc.
- Run A/B tests: It’s time to A/B test your ideas against the existing designs to see if there will be an uplift.
- Document your learnings and iterate: Every A/B test has a result; it’s not about whether a test won, but what did you learn? How does it impact your next test? Also, repeat the cycle. It could be going on the next test or iterating on the just-finished test.
But how will you go about it?
The best way to conduct this sort of website analysis is by using an all-in-one conversion optimization tool.
For example, you can use Figpii to view heatmaps and session recordings, and even run on-site surveys—all under one dashboard.
4. Usability Analysis
A usability analysis is about evaluating a website’s interface to see how online visitors respond.
Usability analysis of your website can be conducted in two critical areas: functionality assessment and expert review.
Functionality assessment:
Functionality assessment requires answers to three important questions:
Are the website functions discoverable?
Can my website visitors use those website functions easily?
Are the links/buttons working?
If your target audience finds a function on your website difficult to use, it will only add to their frustration, leading to a negative experience and users never returning.
You can use tools like Qualaroo, Usabillia, and User testing to conduct this type of website analysis.
Expert review:
Also known as heuristic analysis, the expert review helps detect issues with a website design and helps create educated changes to improve site usability.
To conduct an expert review of your website, you should use the heuristics developed by Jakob Nielsen and actively look for any violations of these rules in your site’s design or functionality.
Jakob Nielsen’s heuristics are:
- Visibility of System Status: Keep users informed about what’s going on through appropriate feedback within a reasonable time.
- Match between the System and the Real World: Use language and concepts familiar to the user, following real-world conventions.
- User Control and Freedom: Provide users with the ability to undo and redo actions, offering an ’emergency exit’ where needed.
- Consistency and Standards: Ensure that the interface follows platform and industry conventions and standards.
- Error Prevention: Design the system to prevent errors from occurring in the first place.
- Recognition Rather Than Recall: Minimize the user’s memory load by making objects, actions, and options visible.
- Flexibility and Efficiency of Use: Accommodate novice and expert users by allowing customization and shortcuts.
- Aesthetic and Minimalist Design: Avoid clutter by including only necessary information in the design.
- Help Users Recognize, Diagnose, and Recover from Errors: Provide clear error messages and guidance for resolving issues.
- Help and Documentation: Offer easily accessible, concise help and documentation when needed.
You can also use tools to assist in your heuristic analysis, such as the Chrome extension UX check and Heurix.
5. Content Analysis
This involves examining the quality, relevance, and SEO optimization of the website’s content. Content should be informative, engaging, and aligned with the target audience’s interests.
What Is Customer Led Website Analysis?
Since our focus will be more on customer-led website analysis than regular website analysis, what exactly is it, and how is it different from a normal website analysis?
Customer-led website analysis is when you evaluate your website from the lens of your site visitors.
This means the focus of your website analysis and optimization isn’t based solely on external audits like competitor analysis, web traffic, or SEO. Instead, you’re investigating your site visitors, looking at how they got to your site, finding out what they want from it, their experience on your site, etc.
Key differences between customer-led website analysis and regular website analysis include:
- User-Centric Approach: Customer-led analysis emphasizes the user’s perspective, focusing on their experience and satisfaction.
- Behavioral Insights: It involves studying user behavior on the site, such as navigation patterns, click-through rates, and engagement with content.
- Feedback Integration: This approach often incorporates direct feedback from users, such as surveys or user testing, to identify areas for improvement.
- Personalization Analysis: Customer-led analysis looks at how well the site personalizes the user experience based on individual preferences and history.
Behavior analytics tools like Figpii will come in handy here.
For example, FigPii will help you understand your customers better and answer important questions like:
- Which elements are they interacting with or ignoring on your web pages?
- Which portion of your web pages do they fall off?
- What do they want from your website?
To help with these questions, Figpii has a unique set of tools
- Heatmaps and Session Recording. Heatmaps and session recordings help you see and understand how users behave on your site. With heatmaps, you can see where visitors click, the elements with the most clicks, the most ignored, and where they’re scrolling past.
- Feedback and Voice of Customer Tools: Figpii also has a poll and survey tool that helps you get mass feedback from your site visitors. You can get user responses in real-time about what they like, what’s not working, and what you can improve.
Using these tools helps you better understand your website experience from the user perspective, and implementing the changes puts the competitive landscape in your favor.
How to Conduct a Comprehensive Website Analysis for SEO and Performance Optimization
We’ve come a long way in figuring out the different types of website analysis and tools you can use to make your analysis easier and more effective.
In this section, we’ll examine how to run a website analysis:
1. Define the objective of your website analysis:
Conducting a website analysis without a goal or focus sets up your analysis for failure.
Maybe you recently noticed a drop in page rankings for some of your web pages or higher cart abandonment rates; these are good enough baselines to start a website analysis.
If you don’t have a clearly defined analysis goal, you risk searching for a needle in a haystack, i.e., you don’t know what you’re analyzing for and how to get it.
2. Choose the right website analysis tools
Understanding the tools available for website analysis can help you optimize your site more effectively.
Here’s an overview of the tools that will prove to be helpful in different parts and aspects of website analysis:
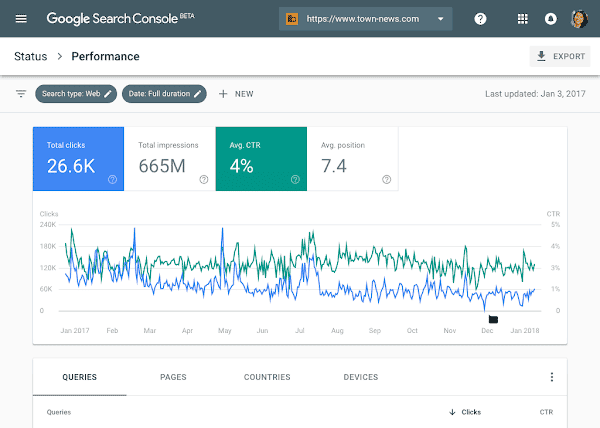
- Google Search Console (GSC): A free search engine optimization tool by Google for monitoring website performance in search results, diagnosing SEO issues, verifying page indexing, and analyzing backlinks and keyword rankings.
- SE Ranking: An all-in-one website SEO checker and a comprehensive website audit tool. It assesses your site using 120+ parameters and provides detailed reports, sitemap generation, and more.
- Screaming Frog SEO Spider: A powerful crawler for conducting a technical SEO audit, traffic analysis, identifying broken links, generating XML sitemaps, and analyzing metadata and meta tags.
- Ahrefs Site Audit Tool: Known for its user-friendly interface, Ahrefs detects over 100 technical issues and groups them into easy-to-understand reports.
- Google PageSpeed Insights: A free tool that analyzes webpage loading speed and provides suggestions for improvement based on real user data from the Chrome browser.
- Pingdom Speed Test: Another tool for testing page speed, grading pages from 0 to 100, and providing key metrics pertaining to your website’s performance. It’s free and doesn’t require login.
Tools for Conversion Rate Optimization (CRO) Analysis:
- All-in-one CRO Tools (e.g., Figpii): Tools like Figpii use session recording and heatmaps to understand user behavior, providing insights for website improvements and conversion optimization.
- Web Analytics Tools (e.g., Google Analytics): Google Analytics offers detailed insights into website traffic, user demographics, and behavior. It’s free but requires embedding a code into your website’s HTML.
- User Behavior Platforms (e.g., FullStory): Platforms like FullStory capture every user interaction on your website, providing insights into user behavior and potential issues.
Tools for Usability Analysis:
- Userfeel: Offers usability testing in over 40 languages, providing features like unmoderated and moderated tests, high-quality tester panels, and video clips.
- TryMyUI: Allows testing of wireframes or prototypes in remote studies, with options to use their participant database or bring your own. Features include test setup, user-narrated videos, and post-test surveys.
3. Create an analysis roadmap:
The next step after creating your analysis goal is to define a roadmap. This step includes benchmark data on conversion rates from your niche.
This helps you determine what exactly you hope to achieve from your analysis.
The next stage is to create a rough step-by-step plan for how you expect your ideal audience to move through your funnel.
Getting as precise as possible in each step and starting as early as possible in your conversion funnel is advantageous.
4. Collect and analyze data:
Your website analysis goal is set; you’ve mapped out the ideal customer journey , and now it’s time to use the tools already discussed to collect data on your website visitors.
Note that the data you collect is dependent on your analysis goal. If your analysis goal is to improve SEO rankings, you may analyze keyword rankings, CTR, impressions, etc.
5. Work on loopholes:
After reviewing the data and seeing what’s working and not working too well, it’s time to double down on the areas that need improvement.
Working with the example from the previous point, if your analysis goal is to improve SEO rankings, you might find that you’re getting fewer impressions on your content or a higher bounce rate on articles.
You can now work on ranking for more relevant content that brings in the right traffic to your website.
6. Make website analysis a habit:
Now that you know the steps to analyze your website, the discussion does not end here.
For your website to remain relevant to visitors and rank on Google, you must consistently have different analysis goals you’re trying to improve.
This way, your website is delivering the best experience possible.
Competitive Analysis: Yes or No?
If you’ve researched this topic, you’ll notice a divide online about competitor website analysis .
For some, it’s a necessary part of website analysis; for others, it’s a different topic all in itself; just focus on your website and how to improve it across different areas.
We can agree that conducting a website analysis is not an activity that’s a walkover in the park.
Since this is true, will adding the task of conducting competitor website analysis be okay?
Logically looking at it, in your niche, you’ve got competition that your audience visits their website to browse and even purchase from.
Following the same logic, it’ll be in your business interest to occasionally conduct competitor website analysis to gain insight into your competitor’s strategy.
Here are three areas you can study on your competitor’s website;
1. Organic traffic:
Many businesses rely on organic traffic to drive long-term growth and repeat online visitors.
Understanding your competitor’s SEO and SERP ranking helps you discover keywords and content you can rank for to attract more relevant traffic. You can use several tools here, like Ahrefs and Semrush.
2. Customer demographics:
Getting an insight into your competitor’s customers gives you ideas of an underserved segment of customers in your niche or a market no one has yet to consider. With tools like Similarweb, you can see your competitor’s global ranking, audience demographics, interests, etc.
Many businesses run ads to supplement their organic efforts. If your competitors have seen good progress in their campaigns, you can study their ad funnel, creatives, audience segment, etc. Focusing on these areas can help improve your paid campaign initiative, too.
An amazing tool you can use here is iSpionage. You can see how many PPC ads your competitors are running, for how long, which keywords they’re bidding on, etc.
Wrapping Up: The Power of Comprehensive Website Analysis
To stay ahead of the competition and ever-changing trends, analyzing the performance of your entire site is a must for your business.
Remember, you don’t conduct a website analysis for analysis’s sake; you must have a goal in mind, something you want to improve.
This way, you satisfy your customers and online visitors, and your website and content continue ranking in search engines.
Remember to leverage behavior analysis and CRO tools like FigPii to assist you in making website analysis easier and more effective.
Share This Article
Join 25,000+ marketing professionals.
Subscribe to Invesp’s blog feed for future articles delivered to receive weekly updates by email.
Discover Similar Topics
Tips and Best Practices for Writing Better Ad Copy
- Copywriting
Mobile Optimization: Increasing Conversions on Small Screens

Our Services
- Conversion Optimization Training
- Conversion Rate Optimization Professional Services
- Landing Page Optimization
- Conversion Rate Audit
- Design for Growth
- Conversion Research & Discovery
- End to End Digital Optimization
By Industry
- E-commerce CRO Services
- Lead Generation CRO Services
- SaaS CRO Services
- Startup CRO Program
- Case Studies
- Privacy Policy
- © 2006-2020 All rights reserved. Invesp
Subscribe with us
- US office: Chicago, IL
- European office: Istanbul, Turkey
- +1.248.270.3325
- [email protected]
- Conversion Rate Optimization Services
- © 2006-2023 All rights reserved. Invesp
- Popular Topics
- A/B Testing
- Business & Growth
- Infographics
- Landing Pages
- Sales & Marketing

Explore all things Poetry
Any poem, any poet, any term..
More results...
Used by 90 Million+ People
Instantly Understand Poetry
“ Easiest, most enjoyable way to learn poetry, period. “
Download Poem PDF Guides
Unlock Exclusive Analysis
Ad-Free Experience
Join Poetry +
Already a Poetry + User? Log in
Explore different poetry
Explore the greatest poets and their poems.

Need to understand a specific poem? Request it
Do you want or need a poem analyzed or help with understanding it? We can help you with just that.
Learn every literary term like never before
We’ve helped explain 905 terms embedded in all our content and guides.
Explore More with Poem Analysis
Dive deep into poetry, whatever direction you may take.
Famous Poems Worth Reading
Not sure where to start? See our pick of some of the best poems ever created, or find a poem using our Poem Explorer Tool or the Poetry Archives .

Because I could not stop for Death
Emily dickinson.

Rudyard Kipling

Still I Rise
Maya angelou.

I Wandered Lonely as a Cloud
William wordsworth.
William E. Henley

Mary Oliver

Edgar Allan Poe

The Hill We Climb
Amanda gorman.

The Love Song of J. Alfred Prufrock

All the World’s a Stage
William shakespeare.

William Blake
The Road Not Taken
Robert frost.

Dover Beach
Matthew arnold.

The Charge of the Light Brigade
Alfred lord tennyson.

Stopping by Woods on a Snowy Evening
Our latest analyses.

They Went Home

The Call of the River Nun
Gabriel okara.

Odysseus’ Decision
Louise glück.

Vespers [In your extended absence, you permit me]
![critical analysis websites Matins [The sun shines; by the mailbox, leaves] by Louise Glück Visual Representation](https://ei7cr2pn3uw.exactdn.com/wp-content/uploads/2024/07/Matins-The-sun-shines-by-the-mailbox-leaves-by-Louise-Gluck-Visual-Representation.jpg?strip=all&lossy=1&ssl=1)
Matins [The sun shines; by the mailbox, leaves]
Changing the world together.
We believe in helping the world, so we have chosen these charities to donate to every month.

Teenage Cancer Trust

Alzheimer’s Research

Great Ormond Street Hospital
Ocean conservancy.

World Animal Protection
Help Center
Request an Analysis
(not a member? Join now)
Poem PDF Guides
PDF Learning Library
Poetry + Newsletter
Poetry Archives
Poetry Explained
Poet Biographies
Useful Links
Poem Explorer
Poem Generator
Poem Solutions Limited, International House, 36-38 Cornhill, London, EC3V 3NG, United Kingdom
Get the Reddit app
This is a moderated subreddit. It is our intent and purpose to foster and encourage in-depth discussion about all things related to books, authors, genres, or publishing in a safe, supportive environment. If you're looking for help with a personal book recommendation, consult our Weekly Recommendation Thread, Suggested Reading page, or ask in r/suggestmeabook.
Best sites to find in depth literary analysis of books?
Recently read "How to Read Literature Like a Professor" and was curious if there are sites that have this level of depth when it comes to analyzing single texts. I am taking AP Literature this year and would love to be able to read these types of analysis to hone my skills, but if that doesn't exist and anyone else has some good tips that would be great.
- Back to main menu
- BROWSE BY TOPIC BROWSE BY TOPIC
- Global IT Asset Management
- IT Security
- Cloud & Container Security
- Web App Security
- Certificate Security & SSL Labs
- Developer API
- Cloud Platform
- Start a discussion
regreSSHion: Remote Unauthenticated Code Execution Vulnerability in OpenSSH server
Last updated on: July 3, 2024
Table of Contents
About openssh: securing enterprise communications and infrastructure, affected openssh versions:, potential impact of regresshion, immediate steps to mitigate risk, technical details, qualys qid coverage, discover vulnerable assets using qualys cybersecurity asset management (csam), enhance your security posture with qualys vulnerability management, detection, and response (vmdr).
- Gain exposure visibility and remediation tracking with the regreSSHion Unified Dashboard
- Automatically Patch regreSSHion vulnerability With Qualys Patch Management
Detect and remediate CVE-2024-6387 with Qualys TotalCloud Container Security
Qualys products and customer responsibilities, frequently asked questions (faqs).

The Qualys Threat Research Unit (TRU) has discovered a Remote Unauthenticated Code Execution (RCE) vulnerability in OpenSSH’s server (sshd) in glibc-based Linux systems. CVE assigned to this vulnerability is CVE-2024-6387.
The vulnerability, which is a signal handler race condition in OpenSSH’s server (sshd), allows unauthenticated remote code execution (RCE) as root on glibc-based Linux systems; that presents a significant security risk. This race condition affects sshd in its default configuration.
Based on searches using Censys and Shodan, we have identified over 14 million potentially vulnerable OpenSSH server instances exposed to the Internet. Anonymized data from Qualys CSAM 3.0 with External Attack Surface Management data reveals that approximately 700,000 external internet-facing instances are vulnerable. This accounts for 31% of all internet-facing instances with OpenSSH in our global customer base. Interestingly, over 0.14% of vulnerable internet-facing instances with OpenSSH service have an End-Of-Life/End-Of-Support version of OpenSSH running.
In our security analysis, we identified that this vulnerability is a regression of the previously patched vulnerability CVE-2006-5051, which was reported in 2006. A regression in this context means that a flaw, once fixed, has reappeared in a subsequent software release, typically due to changes or updates that inadvertently reintroduce the issue. This incident highlights the crucial role of thorough regression testing to prevent the reintroduction of known vulnerabilities into the environment. This regression was introduced in October 2020 (OpenSSH 8.5p1).
Qualys has developed a working exploit for the regreSSHion vulnerability. As part of the disclosure process, we successfully demonstrated the exploit to the OpenSSH team to assist with their understanding and remediation efforts. We do not release our exploits, as we must allow time for patches to be applied. However, even though the exploit is complex, we believe that other independent researchers will be able to replicate our results.
OpenSSH (Open Secure Shell) is a suite of secure networking utilities based on the Secure Shell (SSH) protocol, which is vital for secure communication over unsecured networks. It provides robust encryption to ensure privacy and secure file transfers, making it an essential tool for remote server management and secure data communication. Known for its extensive security and authentication features, OpenSSH supports various encryption technologies and is standard on multiple Unix-like systems, including macOS and Linux.
OpenSSH’s implementation serves as a critical tool for secure communication. Its enterprise value lies in its scalability and the ability to enforce robust access controls and secure automated processes across various environments. This includes everything from automated backups and batch processing to complex DevOps practices, which involve the secure handling of sensitive data across multiple systems and locations. Its continued development and widespread adoption highlight its importance in maintaining the confidentiality and integrity of network communications worldwide.
OpenSSH stands as a benchmark in software security, exemplifying a robust defense-in-depth approach. Despite the recent vulnerability, its overall track record remains exceptionally strong, serving as both a model and an inspiration in the field.
- OpenSSH versions earlier than 4.4p1 are vulnerable to this signal handler race condition unless they are patched for CVE-2006-5051 and CVE-2008-4109.
- Versions from 4.4p1 up to, but not including, 8.5p1 are not vulnerable due to a transformative patch for CVE-2006-5051, which made a previously unsafe function secure.
- The vulnerability resurfaces in versions from 8.5p1 up to, but not including, 9.8p1 due to the accidental removal of a critical component in a function.
OpenBSD systems are unaffected by this bug, as OpenBSD developed a secure mechanism in 2001 that prevents this vulnerability.
This vulnerability, if exploited, could lead to full system compromise where an attacker can execute arbitrary code with the highest privileges, resulting in a complete system takeover, installation of malware, data manipulation, and the creation of backdoors for persistent access. It could facilitate network propagation, allowing attackers to use a compromised system as a foothold to traverse and exploit other vulnerable systems within the organization.
Moreover, gaining root access would enable attackers to bypass critical security mechanisms such as firewalls, intrusion detection systems, and logging mechanisms, further obscuring their activities. This could also result in significant data breaches and leakage, giving attackers access to all data stored on the system, including sensitive or proprietary information that could be stolen or publicly disclosed.
This vulnerability is challenging to exploit due to its remote race condition nature, requiring multiple attempts for a successful attack. This can cause memory corruption and necessitate overcoming Address Space Layout Randomization (ASLR). Advancements in deep learning may significantly increase the exploitation rate, potentially providing attackers with a substantial advantage in leveraging such security flaws.
Addressing the regreSSHion vulnerability in OpenSSH, which enables remote code execution on Linux systems, demands a focused and layered security approach. Here are concise steps and strategic recommendations for enterprises to safeguard against this significant threat:
- Patch Management : Quickly apply available patches for OpenSSH and prioritize ongoing update processes.
- Enhanced Access Control : Limit SSH access through network-based controls to minimize the attack risks.
- Network Segmentation and Intrusion Detection : Divide networks to restrict unauthorized access and lateral movements within critical environments and deploy systems to monitor and alert on unusual activities indicative of exploitation attempts.
- Custom Assessment and Remediation: Quickly execute mitigation script on required assets. To find out more, check out the FAQ section ‘Are there any mitigations for this vulnerability?’
You can find the technical details of this vulnerability at:
https://www.qualys.com/2024/07/01/cve-2024-6387/regresshion.txt
Qualys is releasing the QIDs in the table below as they become available, starting with vulnsigs version VULNSIGS-2.6.83-4 and in Linux Cloud Agent manifest version LX_MANIFEST-2.6.83.4-5
| 513833 | Alpine Linux 3.20 Security Update for openssh (regreSSHion) | Alpine Linux |
| 513832 | Alpine Linux 3.19 Security Update for openssh (regreSSHion) | Alpine Linux |
| 513831 | Alpine Linux 3.18 Security Update for openssh (regreSSHion) | Alpine Linux |
| 513830 | Alpine Linux 3.17 Security Update for openssh (regreSSHion) | Alpine Linux |
| 285635 | Fedora Security Update for openssh (FEDORA-2024-213f33544e) (regreSSHion) | Fedora Security |
| 756591 | SUSE Enterprise Linux Security Update for openssh (SUSE-SU-2024:2275-1) (regreSSHion) | SUSE Enterprise |
| 357791 | Amazon Linux Security Advisory for openssh : ALAS2023-2024-649 (regreSSHion) | Amazon Linux |
| 710942 | Gentoo Linux OpenSSH Remote Code Execution Vulnerability (GLSA 202407-09) (regreSSHion) | Gentoo Linux |
| 6081987 | VMware Photon OS Security Update for openssh (PHSA-2024-4.0-0642) (regreSSHion) | VMware Photon |
| 6081986 | VMware Photon OS Security Update for openssh (PHSA-2024-5.0-0307) (regreSSHion) | VMware Photon |
| 6122971 | Google Container OS-Optimized OS 101 Security Update for net-misc/openssh (CVE-2024-6387) (regreSSHion) | Google Container OS |
| 6122969 | Google Container OS-Optimized OS 105 Security Update for net-misc/openssh (CVE-2024-6387) (regreSSHion) | Google Container OS |
| 6122965 | Google Container OS-Optimized OS 109 Security Update for net-misc/openssh (CVE-2024-6387) (regreSSHion) | Google Container OS |
| 6122961 | Google Container OS-Optimized OS 113 Security Update for net-misc/openssh (CVE-2024-6387) (regreSSHion) | Google Container OS |
| 161766 | Oracle Enterprise Linux Security Update for openssh (ELSA-2024-12468) (regreSSHion) | Oracle Enterprise |
| 691562 | Free Berkeley Software Distribution (FreeBSD) Security Update for openssh (f1a00122-3797-11ef-b611-84a93843eb75) (regreSSHion) | Free Berkeley |
| 200455 | Debian/Ubuntu Notification for OpenSSH Vulnerability (USN-6859-1) (regreSSHion) | Debian/Ubuntu |
| 6007430 | Debian 11 Security Update for openssh (CVE-2024-6387) (regreSSHion) | Debian 11 Security |
| 6007429 | Debian/Ubuntu Update for openssh (DSA 5724-1) (regreSSHion) | Debian/Ubuntu |
| 42046 | OpenSSH Remote Unauthenticated Code Execution Vulnerability (regreSSHion) | OS agnostic |
| 243964 | Red Hat Update for openssh (RHSA-2024:4312) | Red Hat |
It is recommended that Qualys customers use OS-specific QIDs to scan for backported packages on supported Linux distributions.
Please check the Qualys Vulnerability Knowledgebase for the full list of coverage for this vulnerability.
The initial and crucial step in managing this critical vulnerability and mitigating associated risks involves pinpointing all assets susceptible to this specific issue. Use CSAM 3.0 with External Attack Surface Management to identify your organization’s internet-facing instances that have vulnerable versions of OpenSSH or are at their End of Life (EOL) or End of Support (EOS).
Identify internet-facing instances with vulnerable versions of OpenSSH
In the following example, we aim to identify all assets running the OpenSSH:
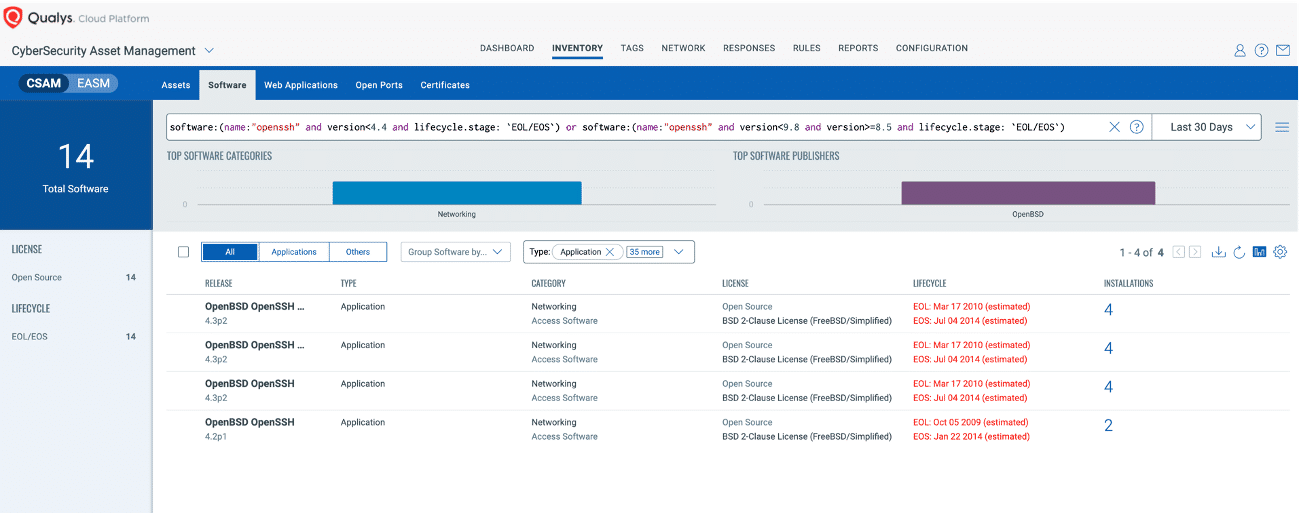
Qualys VMDR offers comprehensive coverage and visibility into vulnerabilities, empowering organizations to rapidly respond to, prioritize, and mitigate the associated risks. Additionally, Qualys customers can leverage Qualys Patch Management to remediate these vulnerabilities effectively.
Leverage the power of Qualys VMDR alongside TruRisk and the Qualys Query Language (QQL) to efficiently identify and prioritize vulnerable assets, effectively addressing the vulnerabilities highlighted above.
Try Qualys VMDR at no cost for 30 days
Use this QQL statement:
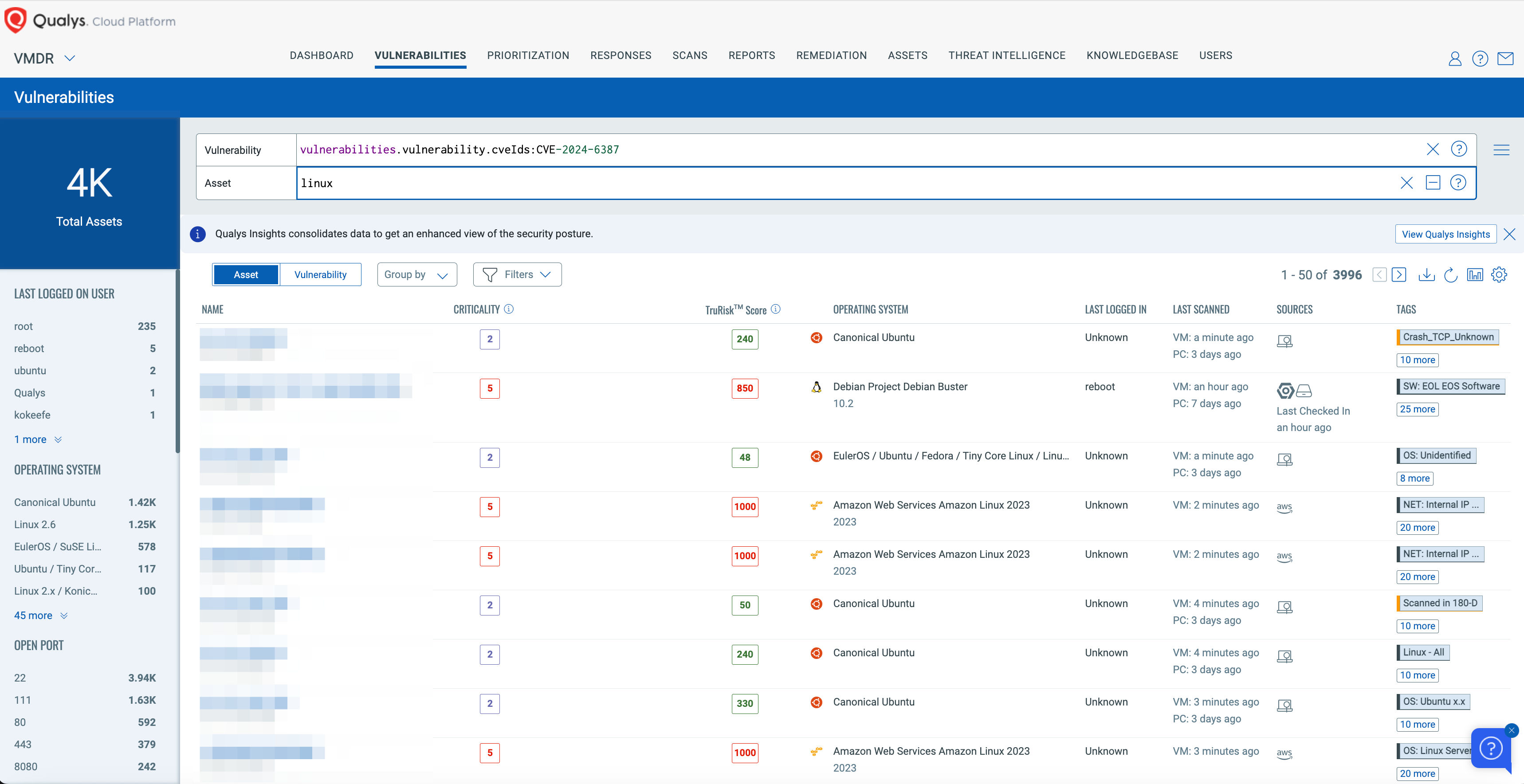
Gain exposure visibility and remediation tracking with the “regreSSHion” Unified Dashboard
With the Qualys Unified Dashboard, you can track the vulnerability exposure within your organization and view your impacted hosts, their status, distribution across environments, and overall management in real time, allowing you to see your mean time to remediation (MTTR).
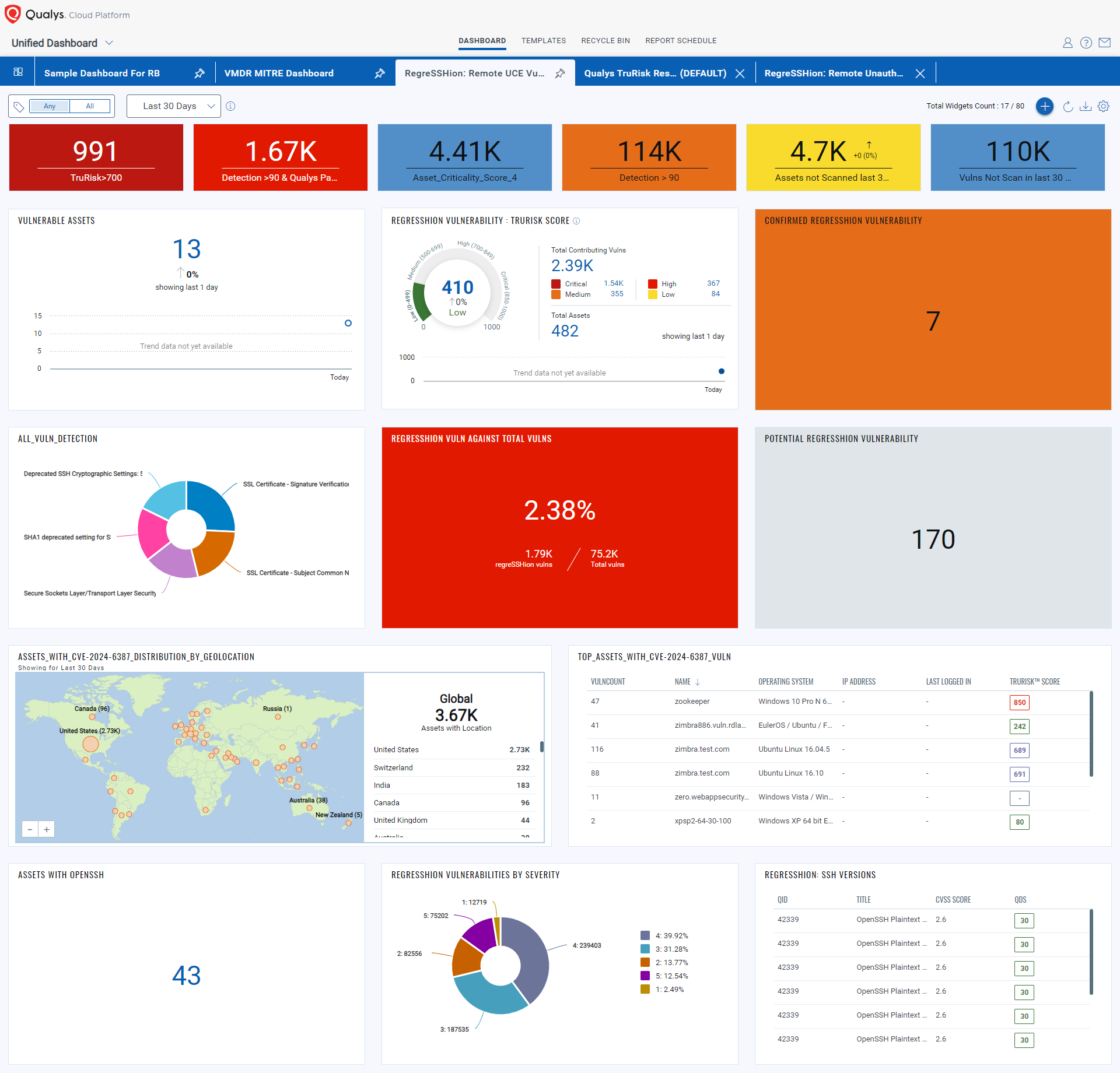
To make it easier for customers to track and manage regreSSHion vulnerability in their subscriptions, we have created the Manage regreSSHion dashboard , which you can download and import into your subscription.
Automatically Patch “regreSSHion” vulnerability With Qualys Patch Management
We expect vendors to release patches for this vulnerability shortly. Qualys Patch Management can automatically deploy those patches to vulnerable assets, when available.
Customers can use the “patch now” button found to the right of the vulnerability to add regreSSHion to a patch job. Once patches are released, Qualys will find the relevant patches for this vulnerability and automatically add those patches to a patch job. This will allow customers to deploy those patches to vulnerable devices, all from the Qualys Cloud Platform.
Qualys Patch Management No-Cost 45-Day Trial
Qualys TotalCloud Container Security offers comprehensive coverage and visibility into vulnerabilities across all your container environments, including managed Kubernetes and on-premises Kubernetes. This empowers organizations to rapidly respond to, prioritize, and mitigate associated risks effectively.
Leverage the power of Qualys TotalCloud Container Security and the Qualys Query Language (QQL) to efficiently identify and prioritize vulnerable assets, ensuring prompt and effective remediation of the vulnerabilities highlighted by CVE-2024-6387.
Qualys is cutting the release cycle short for certain products that are deployed on customer premises. At least one of those products depends on a supplier that will publish a fix release shortly. We intend to release fixes for this Severity HIGH CVE in the coming days to ensure that customers are safe from regreSSHion. Once builds have cleared Quality Assurance, we will provide updates to help customers patch.
Will the Qualys Research Team publish exploit code or include proof-of-concept code for this vulnerability?
No, as part of our commitment to responsible disclosure and maintaining high-security standards, we will not publish exploit codes. Given the complexity of this vulnerability, it is crucial to allow organizations to apply patches effectively without the immediate pressure of public exploits.
Are there any mitigations for this vulnerability?
If sshd can’t be updated or recompiled, set LoginGraceTime to 0 in the config file. This exposes sshd to a denial of service by using up all MaxStartups connections, but it prevents the remote code execution risk.
Using Qualys Custom Assessment and Remediation (CAR), you can easily apply this mitigation across affected assets in one go. Just follow these easy steps:
1. Go to CAR Library, look for Zero Day Utilities, and import the mitigation script.
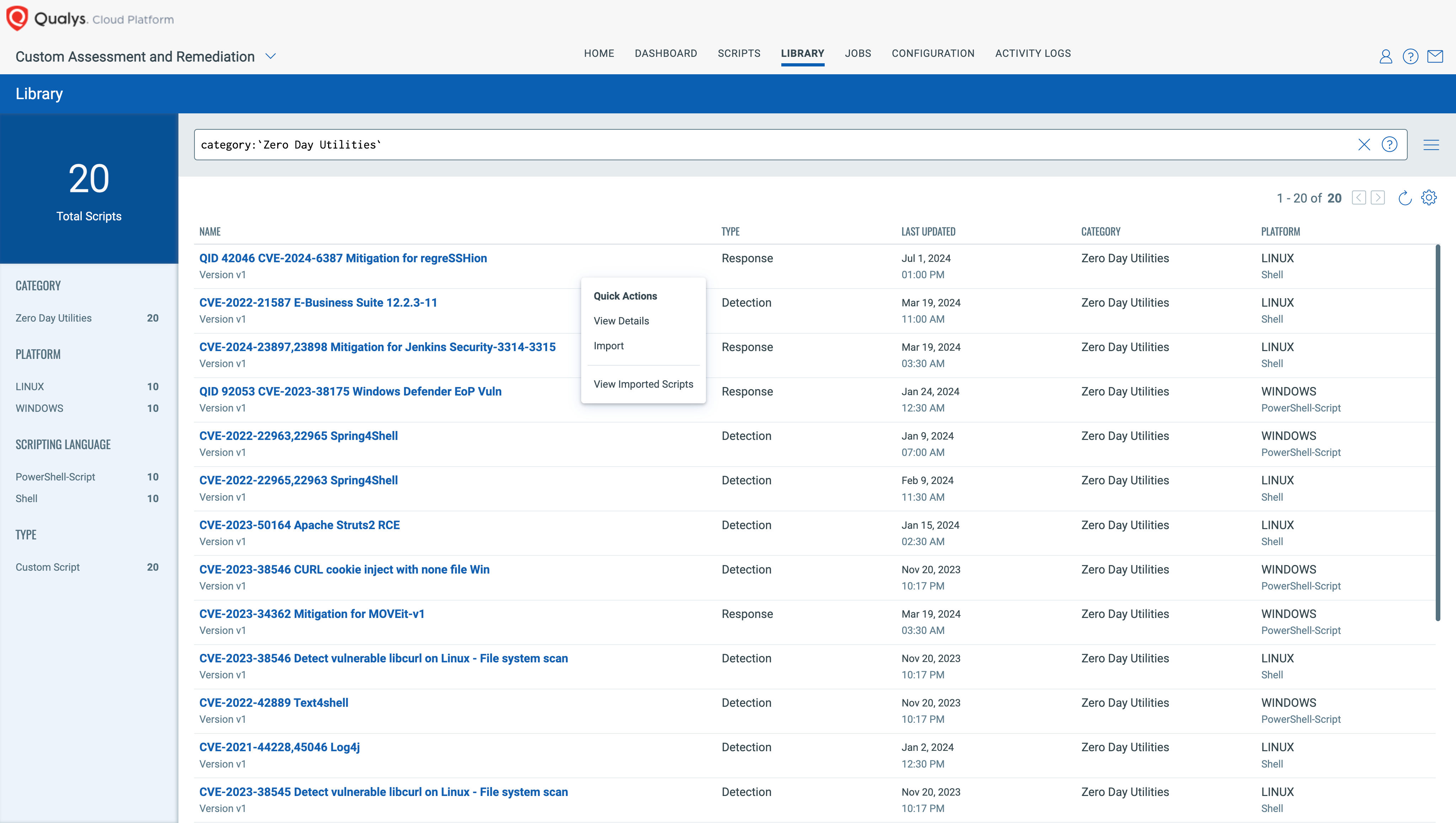
2. You can approve while importing or later on.
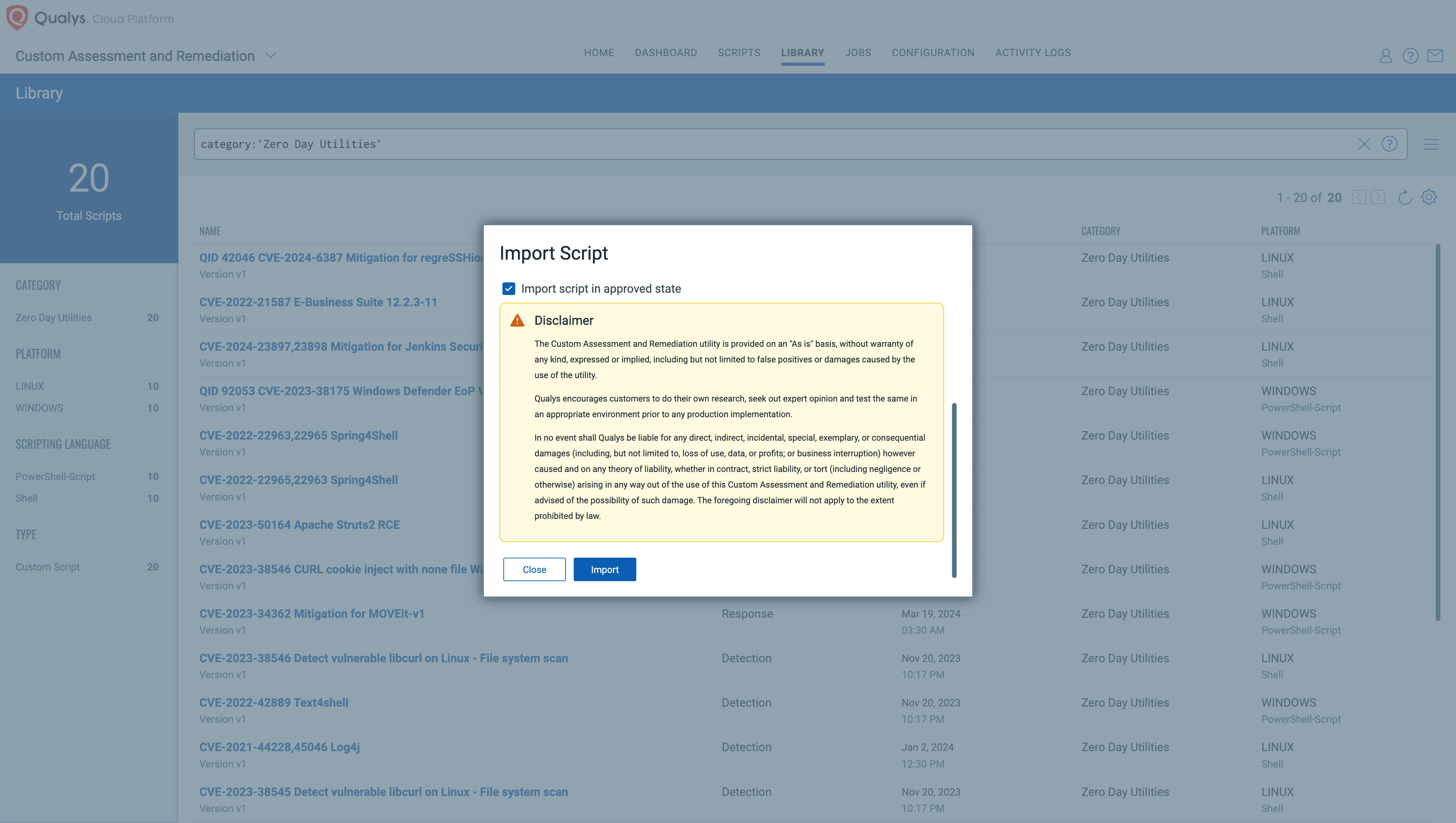
3. Execute it across required assets/asset tags.
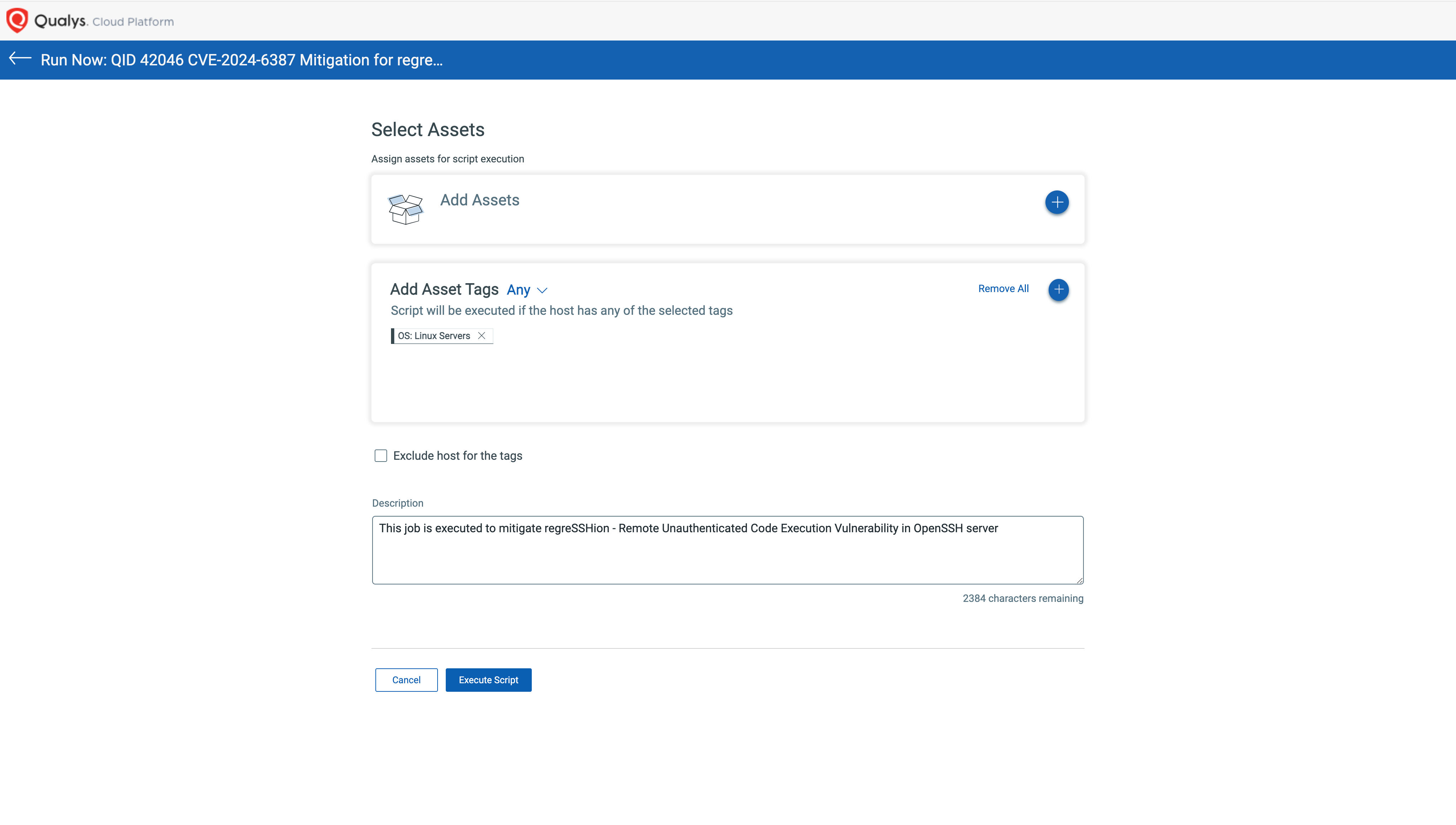
To execute this mitigation, enable your free trial of CAR – https://www.qualys.com/forms/custom-assessment-remediation/
Is this vulnerability remotely exploitable?
Yes, this vulnerability can be exploited remotely and allows unauthenticated remote code execution (RCE) as root, posing a significant security risk.
Why is the vulnerability named “regreSSHion”?
This is a pun/reference to this being a regression bug affecting OpenSSH.
Should organizations patch these vulnerabilities urgently?
Yes, we would encourage organizations to patch this vulnerability urgently, especially on their internet-facing assets.
How will the new security fix be implemented for different versions?
This fix is part of a major update, making it challenging to backport. Consequently, users will have two update options: upgrading to the latest version released on Monday, July 1st (9.8p1) or applying a fix to older versions as outlined in the advisory, which is the approach most vendors will take.
Does this vulnerability affect macOS or Windows?
While it is likely that the vulnerability exists in both macOS and Windows, its exploitability on these platforms remains uncertain. Further analysis is required to determine the specific impact.
How can users identify exploitation attempts of this vulnerability?
Exploitation attempts for this vulnerability can be identified by seeing many many lines of “Timeout before authentication” in the logs.
What is the exposure to Qualys infrastructure?
The Qualys security team has taken immediate steps to protect our corporate infrastructure and products from any impact regarding the exploitation of this vulnerability. At this time, we have not experienced any negative impacts or detected any exploitation attempts. In addition, the Qualys security team has implemented enhanced monitoring and response plans to detect and respond to future exploit attempts. Emergency patching procedures have been initiated to fully remediate the vulnerability. To further help the broader security community, we are sharing our detection logic (see FAQ: “How to identify exploitation attempts of this vulnerability?”) to help customers respond should attacks occur before patching and mitigation efforts are completed.
How can users identify systems vulnerable to the OpenSSH regreSSHion vulnerability?
Users can determine if their systems are vulnerable by verifying the version of the OpenSSH server installed. Systems running affected versions should be considered at risk and prioritized for updates.
Under what circumstances might QID 42046 fail to report accurately?
Accurate detection with QID 42046 requires root privileges, as the command used only runs with root access.
Why is a QID categorized as a confirmed or potential vulnerability?
A QID is reported as confirmed in authenticated scan results because these scans can access detailed information that verifies the vulnerability more reliably. On the other hand, remote unauthenticated scans categorize a QID as potential because they primarily depend on the information presented by the OpenSSH service banner. This banner might display a partial version of details, leading to less definitive conclusions about the presence of a vulnerability.
When will the Qualys Detection Score (QDS) be updated?
As the vulnerability begins to trend across various threat intelligence sources, our QDS will utilize these intelligent feeds for dynamic updates. We expect its effectiveness to reach a score of 90 or above.
Has the threat feed been updated to include the regreSSHion vulnerability?
Yes, the Qualys threat feed is updated when emerging threats are tracked and reported from the dark web and other sources. The update activates as soon as a vulnerability trends across various threat intelligence platforms.
Comments Cancel reply
Your email address will not be published. Required fields are marked *
Save my name, email, and website in this browser for the next time I comment.
No record found for this QID or CVE in Qualys KB. Great job on reporting however the data set is not published.
“Immediate Steps to Mitigate Risk” there’s a config-based mitigation, this section is just marketing nonsense and it’s irresponsible of you to hide the actual immediate mitigation in the “technical details”
More From Forbes
Can chatgpt help you win at poker.
- Share to Facebook
- Share to Twitter
- Share to Linkedin
ChatGPT can give advice on when to bet with poker hands
If you’re an online poker player, a little strategy knowledge can go a long way. There are plenty of poker apps and tutorials out there, but they tend to be expensive. Can ChatGPT fill the void and teach you how to win at poker?
For the past few weeks I’ve been using ChatGPT to analyze my play in online Texas hold ‘em games to see if it can teach me a thing or two about strategy. I’ve read a couple of poker books, watched online tutorials from professional players such as Daniel Negreanu , and played casually for a few years, but I’m by no means a poker expert.
What’s more, I play with low-stakes pocket money, not serious cash, so the opponents I play against are likely to be low-skilled, looser players who care less about making wild bets because the stakes are so low.
To be clear, I’m not advocating gambling nor do I suggest that following ChatGPT’s advice is anything like a get-rich-quick scheme for poker players. But, as illustrated below, there are ways in which ChatGPT can help evaluate your poker game and point out where you’re going right and wrong.
Is ChatGPT Good At Poker?
The first question to ask is whether ChatGPT is even capable of playing poker. After all, it’s an all-purpose chatbot, not an AI specifically trained to play the game, unlike say Google DeepMind’s Alpha Go , which destroyed the world’s best Go players.
Best High-Yield Savings Accounts Of 2024
Best 5% interest savings accounts of 2024.
Thankfully, academics have answered that question. A study published in 2023 by Berkley researcher Askhat Gupta examined how ChatGPT played poker compared to the game theory optimal strategy, which is essentially the best possible strategy for any given hand.
Gupta’s study found that ChatGPT exhibited “advanced understanding of poker, encompassing concepts like the valuation of starting hands, playing positions and other intricacies of game theory optimal poker.”
However, the study found that ChatGPT tended to play conservatively, only betting with premium hands and folding the rest. That low-risk strategy could be easily exploited by other human players, who might detect you only bet with strong hands and thus avoid entering pots you’ve committed to.
That said, it’s worth pointing out that at the time of the study, ChatGPT was running a now outdated AI model. Gupta’s tests with the more recent GPT-4 (a variant of which is still used today) found it to be much more hawkish. “GPT-4 plays like a maniac, showcasing a loose and aggressive style of play,” Gupta’s study found. “Both strategies, although relatively advanced, are not game theory optimal.”
How ChatGPT Can Analyze Your Poker Game
ChatGPT can analyze whether you were right to go all-in
If you’ve clicked on this article hoping to find out how ChatGPT can help you cheat in live games by advising which hands to play, you’ve had a wasted journey. Unless you’re a speed-of-light typist, there’s no way you could enter the required information on blinds, pot size, players’ pots, bets placed and cards dealt in time to get answers during a live game. There’s no doubt AI bots are already being used in online poker, but this isn’t a guide to using them.
Instead, ChatGPT comes into its own when analyzing your performance in games you’ve already played, hopefully helping you to improve your decision making for next time.
Online poker services, such as the GG Poker site I use, normally give you the option to download plain text histories of the hands you’ve played in tournaments or cash games. These can be uploaded to ChatGPT, from where you can ask the AI to rate how you played.
With a 60-hand history of a recent cash game I played uploaded to ChatGPT (you click the paperclip icon in the chat window to upload files), I entered the following prompt:
Here's my hand history for a no-limit Texas hold 'em session. Analyse my play.
This delivered a detailed analysis of three hands that I played, offering an opinion on whether I was wise to place the bets I did at the various stages of the hand (pre-flop, flop, turn and river), as well as strategic advice on each hand and an overall summary.
For example, in a hand picked out by the AI, where I’d bluffed the river (the final bet of the hand) with a large bet that prompted my opponent to fold, ChatGPT advised me to “ensure your bluffs are balanced with value bets in similar situations to avoid predictability,” which is pretty sound advice that I’ve read elsewhere in the poker guides.
ChatGPT can also be called upon to analyze individual hands where you’ve won big or lost heavily, to review whether you made the correct calls. Just because you scooped a big pot it doesn’t mean you played it well, and “bad beats” where you lose with the strongest hands are also common.
So, with your hand history uploaded, you might ask ChatGPT:
Examine the hand in which I won the most money
Analyze the hand in which I lost the most money
The hand in which I suffered the biggest loss was actually one in which I had a very strong opening hand—a pair of kings. However, an ace appeared on the turn, prompting my opponent to place a sizeable bet, suggesting they might have a kings-beating pair of aces now. With no other kings or straight/flush possibilities arriving on the river, I decided to fold when my opponent made an even larger bet.
ChatGPT advised that my “fold is cautious but reasonable given the large bet and potential holdings of the Big Blind.” So, no need to feel too bad about that costly hand.
Advanced Analysis
ChatGPT’s coding ability lets you take the poker hand analysis even further.
There’s a GPT in the ChatGPT store called Poker Hand Analyzer , which promises to analyze hands using a Monte Carlo simulation—basically running potential hands many times to obtain a numeric probability of success or failure. A GPT, for those who don’t know, is a chatbot within ChatGPT that’s dedicated to a specific task, such as booking travel tickets, answering math problems or, in this case, helping you to improve your poker skills.
I asked Poker Hand Analyzer to run a Monte Carlo simulation on my pair of kings hand above, to get a more detailed analysis of whether I was right to fold that strong hand.
To do this, the GPT first defines a plausible range of cards that my opponent might have in his hand. Of course, this being a low-stakes game with amateur players, he could have literally anything, but the AI makes assumptions based on the way the opponent made his bets. By the time we got to the river, the AI assumes the opponent is holding either a strong hand (ie. suited Ace-Jack) or a missed draw that he’s trying to bluff with.
It then generates code in Python for that specific hand, which will be run against the treys poker hand evaluation library. ChatGPT can’t run this program itself, but it provides me with full instructions on how to install Python, the treys library and how to run the code. Note that even with these instructions, this is a reasonably techy process that will likely require advanced computer skills.
After a couple of code revisions to overcome error messages (all handled by the AI), we finally get a running Monte Carlo simulation of my hand, and it reckons my pair of kings would have won 51.6% of the time. In other words, I was in a coin toss. The fold was conservative, but not ridiculously so.
For comparison, I put the same hand information into the PokerNews Odds Calculator and it reckons I had a 60.3% chance of winning the hand with the kings. But it has less information to work with. It hasn’t created a shortlist of likely opponent hands based on the betting patterns up to the river, for example.
Still, armed with all of this information, I might be more tempted to back myself in a similar situation next time.
ChatGPT’s Poker Flaws
The majority of the poker advice I’ve been given by ChatGPT seems sound, and is roughly consistent with that provided by the books I’ve read or the professionals’ videos. Its ability to analyze hands I’ve played and spot errors in my play is a huge help. For example, it’s helped me correct a flaw where I wasn’t spotting the potential for opponents to make a straight, meaning that I was often over-betting with weaker hands, such as two pairs.
That said, I don’t think ChatGPT’s advice is going to win me a bracelet at the next world championships. It’s good for correcting basic errors and monitoring past performance, but it’s not going to transform me—a distinctly amateur player—into Daniel Negreanu.
It’s also prone to the odd basic error itself. For example, in one analysis it describes my hand of seven of spades and five of hearts as a “suited connector”, when in fact it’s an unsuited connector—two cards of different suits that could form part of a straight draw (ie. 5,6,7,8,9).
That kind of basic error undermines confidence in its advice, although it doesn’t invalidate it entirely. I’m probably not going to become a poker millionaire with ChatGPT’s help, but I probably wouldn’t become one with Daniel Negreanu’s help, either.

- Editorial Standards
- Reprints & Permissions
Join The Conversation
One Community. Many Voices. Create a free account to share your thoughts.
Forbes Community Guidelines
Our community is about connecting people through open and thoughtful conversations. We want our readers to share their views and exchange ideas and facts in a safe space.
In order to do so, please follow the posting rules in our site's Terms of Service. We've summarized some of those key rules below. Simply put, keep it civil.
Your post will be rejected if we notice that it seems to contain:
- False or intentionally out-of-context or misleading information
- Insults, profanity, incoherent, obscene or inflammatory language or threats of any kind
- Attacks on the identity of other commenters or the article's author
- Content that otherwise violates our site's terms.
User accounts will be blocked if we notice or believe that users are engaged in:
- Continuous attempts to re-post comments that have been previously moderated/rejected
- Racist, sexist, homophobic or other discriminatory comments
- Attempts or tactics that put the site security at risk
- Actions that otherwise violate our site's terms.
So, how can you be a power user?
- Stay on topic and share your insights
- Feel free to be clear and thoughtful to get your point across
- ‘Like’ or ‘Dislike’ to show your point of view.
- Protect your community.
- Use the report tool to alert us when someone breaks the rules.
Thanks for reading our community guidelines. Please read the full list of posting rules found in our site's Terms of Service.

IMAGES
VIDEO
COMMENTS
The Literary Film & TV You Need to Stream in June Summertime, and the Streaming's Easy. May 31, 2024. Read Full Story. 18 New Novels You Need to Read This Summer More Light, More Books. May 29, 2024. Read Full Story. Remembering Paul Auster 1947-2024. May 28, 2024. Read Full Story.
Cambridge History of English and American Literature contains over 300 chapters with essay topics ranging from poetry, fiction, drama and essays to history, theology and political writing. Small but growing site of literature guides for works commonly used in high school and college classes. This site, managed by a company called SuperSummary ...
The Destination for Literary Research. Gale Literature Resource Center is Gale's most current, comprehensive, and reliable online literature resource, offering the broadest and most representative range of authors and their works, including a deep collection of full-text critical and literary analysis for literary studies.The resource provides researchers with unbounding literary resources ...
Detailed explanations, analysis, and citation info for every important quote on LitCharts. The original text plus a side-by-side modern translation of every Shakespeare play. ... Definitions and examples of 136 literary terms and devices. Instant PDF downloads. Refine any search. Find related themes, quotes, symbols, characters, and more.
Gale | 2020 | ISBN-13: 9781410394477. Contemporary Literary Criticism (CLC) compiles analysis of the writings of the world's most renowned novelists, poets, playwrights, short story writers, scriptwriters, and other creative writers. CLC also provides supplementary biographical context and bibliographic material to guide the reader to a ...
Critical Analysis Format is as follows: I. Introduction. Provide a brief overview of the text, object, or event being analyzed. Explain the purpose of the analysis and its significance. Provide background information on the context and relevant historical or cultural factors. II.
Literary analysis is a written evaluation of the elements of a literary work, for example, a poem, short story, novel, etc. It aims to deepen one's understanding of the work's ideas and impact on the readers. Literary analysis is not just about summarizing what you read . It involves deconstructing the artwork to evaluate its parts, including ...
Allows you to search for primary texts, such as short stories, poems, and novels. Also includes author biographies. Over 36,000 eBooks available to download. Search for literary works and primary texts. Browse poems by title, author, or time period. Site also contains interviews, articles, and podcasts. Search the archive by author name or ...
Explore the database of book analysis, summaries and reviews, and author information on the internet. Any Book. Any Author. Understand them all. ... Our expert team dives deep into the literary realm to bring you comprehensive summaries and analyses. From students to book lovers, we have something for everyone. About Book Analysis.
How to Write a Critical Analysis Essay. Written by MasterClass. Last updated: Jun 7, 2021 • 3 min read. Critical analysis essays can be a daunting form of academic writing, but crafting a good critical analysis paper can be straightforward if you have the right approach.
Critical Analysis of the Content. Having made an initial appraisal, you should now examine the body of the source. Read the preface to determine the author's intentions for the book. Scan the table of contents and the index to get a broad overview of the material it covers. Note whether bibliographies are included.
Novelguide.com is the premier free source for literary analysis on the web. We provide an educational supplement for better understanding of classic and contemporary literature. Novelguide.com is continually in the process of adding more books to the website each week. Please check back weekly to see what we have added.
Analysis of Albert Camus's The Plague. By NASRULLAH MAMBROL on August 4, 2023. The Plague was written by Albert Camus (1913-60), one of the most gifted and influential writers and philosophers in the French language of the 20th century. He was awarded the Nobel Prize in literature in 1957. Camus was born in….
To evaluate something or someone, you think and consider it or them in order to make a judgment about it/them; this could be as simple as how good or bad they are. When you critically evaluate something or someone you consider how judgments vary from different perspectives and how some judgments are stronger than others. This often means ...
A critical analysis is an argument about a particular piece of media. There are typically two parts: (1) identify and explain the argument the author is making, and (2), provide your own argument about that argument. Your instructor may have very specific requirements on how you are to write your critical analysis, so make sure you read your ...
Therefore, your critical analysis might focus not just on language, but also on design, layout, and visuals. Developed by Learning Advisers 2022 2 Writing critically about a website Once you have critically analysed the website using appropriate critical thinking questions, use your notes to form written paragraphs which demonstrate your ...
Enago Read - Research assistant tool helps with literature review, critical analysis, summarizing, and more. Enago Read - Research assistant tool helps with literature review, critical analysis, summarizing, and more. Refer to help Enago Read get more feedback to keep the magic going! In appreciation, get $12 credits.
Gale Literature Criticism takes literature, history and culture to the next level with the largest, most extensive compilation of literary commentary available.The 10 award-winning series that comprise Gale Literature Criticism represent a range of modern and historical views on authors and their works across regions, eras and genres.. Imagine centuries of analysis—the scholarly and popular ...
2. Performance Analysis. This involves checking the website's speed, loading times, and overall responsiveness. After all, a fast-loading website is indispensable for keeping visitors engaged. For example, Google found that a one-second delay in mobile loading times can impact conversion rates by up to 20%. 3.
Changing the World Together. We believe in helping the world, so we have chosen these charities to donate to every month. A website dedicated to analyzing poetry from past and present, to provide a database of articles to summarize and critically analyze any poem.
Well, take the title you are interested in and look for the scholarly articles for it. Use Google Scholar. Some texts have websites devoted to their exegesis (eg, Ulysses, Finnegans Wake, religious books), but I try to start by using Norton Critical editions for my books if I want to read some criticism.
The Qualys Threat Research Unit (TRU) has discovered a Remote Unauthenticated Code Execution (RCE) vulnerability in OpenSSH's server (sshd) in glibc-based Linux systems. CVE assigned to this vulnerability is CVE-2024-6387.. The vulnerability, which is a signal handler race condition in OpenSSH's server (sshd), allows unauthenticated remote code execution (RCE) as root on glibc-based Linux ...
For example, in one analysis it describes my hand of seven of spades and five of hearts as a "suited connector", when in fact it's an unsuited connector—two cards of different suits that ...
The central component in impactful healthcare decisions is evidence. Understanding how nurse leaders use evidence in their own managerial decision making is still limited. This mixed methods systematic review aimed to examine how evidence is used to solve leadership problems and to describe the measured and perceived effects of evidence-based leadership on nurse leaders and their performance ...
The first showdown between Biden, 81, and Trump, 78, in 2024 comes early in the election year, giving voters an opportunity to see the president and his challenger side-by-side.